Search results for Office Exploited
A Cinematic Tutorial on How to Work With Artificial Intelligence
In reality, there are no streams of ex-employees leaving their offices with boxes of personal belongings in their hands. Among our colleagues, acquaintances, and clients, there is not a single person who has fired an employee or lost his or her job because artificial intelligence has replaced them. On the contrary, there is a consistent shortage of qualified personnel. This includes those who are able to effectively search for and use various AI applications in their work.
A Cinematic Tutorial on How to Work With Artificial...
In reality, there are no streams of ex-employees leaving their offices with boxes...
Source: Hacker Noon
New BIG-IP Next Central Manager bugs allow device takeover

F5 has fixed two high-severity BIG-IP Next Central Manager vulnerabilities, which can be exploited to gain admin control and create rogue accounts on any managed assets. [...]

New BIG-IP Next Central Manager bugs allow device...
F5 has fixed two high-severity BIG-IP Next Central Manager vulnerabilities, which...
Source: BleepingComputer
Kaisen Linux | The distribution for professional IT

Kaisen Linux is a distribution dedicated for IT professional based on Debian GNU/Linux. Large tools are integrated for diagnostics, rescue system and networks, lab creation and many more!

Kaisen Linux | The distribution for professional IT...
Kaisen Linux is a distribution dedicated for IT professional based on Debian GNU/Linux....
LockBitSupp Revealed? - ThreatWire

⬇️ OPEN FOR LINKS TO ARTICLES TO LEARN MORE ⬇️ @endingwithali → Twitch: https://twitch.tv/endingwithali Twitter: https://twitter.com/endingwithali YouTube: https://youtube.com/@endingwithali Everywhere else: https://links.ali.dev [❗] Join the Patreon→ https://patreon.com/threatwire 0:00 Intro 00:00:08 1 - CISA and FBI Release New Developer Warning 00:01:42 2 - GitLab Vuln is Leading to Account Takeovers 00:03:02 3 - Ministry of Defence Hacked 00:04:08 4 - LockBit Troll 00:05:52 Outro LINKS 🔗 Story 1: CISA and FBI Release New Developer Warning https://www.cisa.gov/sites/default/files/2024-05/Secure_by_Design_Alert_Eliminating_Directory_Traversal_Vulnerabilities_in_Software_508c%20%283%29.pdf https://www.bleepingcomputer.com/news/security/cisa-urges-software-devs-to-weed-out-path-traversal-vulnerabilities/ 🔗 Story 2: GitLab Vuln is Leading to Account Takeovers https://www.bleepingcomputer.com/news/security/cisa-says-gitlab-account-takeover-bug-is-actively-exploited-in-attacks/ https://www.cisa.gov/news-events/alerts/2024/01/10/cisa-adds-one-known-exploited-vulnerability-catalog https://www.darkreading.com/application-security/critical-gitlab-bug-exploit-account-takeover-cisa https://thehackernews.com/2024/05/cisa-warns-of-active-exploitation-of.html 🔗 Story 3: Ministry of Defence Hacked https://www.bbc.com/news/uk-68966497 https://news.sky.com/story/china-hacked-ministry-of-defence-sky-news-learns-13130757 https://news.sky.com/story/china-responsible-for-two-cyber-attack-campaigns-in-uk-says-dowden-13101680 🔗 Story 4: LockBit Troll https://twitter.com/NCA_UK/status/1787492550342799746 https://twitter.com/vxunderground/status/1787234502323978385 https://techcrunch.com/2024/05/06/police-resurrect-lockbits-site-and-troll-the-ransomware-gang/ https://twitter.com/vxunderground/status/1787845917803946131/photo/1 https://twitter.com/vxunderground/status/1787854092406083800 ____________________________________________ Founded in 2005, Hak5's mission is to advance the InfoSec industry. We do this through our award winning educational podcasts, leading pentest gear, and inclusive community – where all hackers belong.

LockBitSupp Revealed? - ThreatWire
⬇️ OPEN FOR LINKS TO ARTICLES TO LEARN MORE ⬇️
@endingwithali →
Twitch:...
Source: Hak5
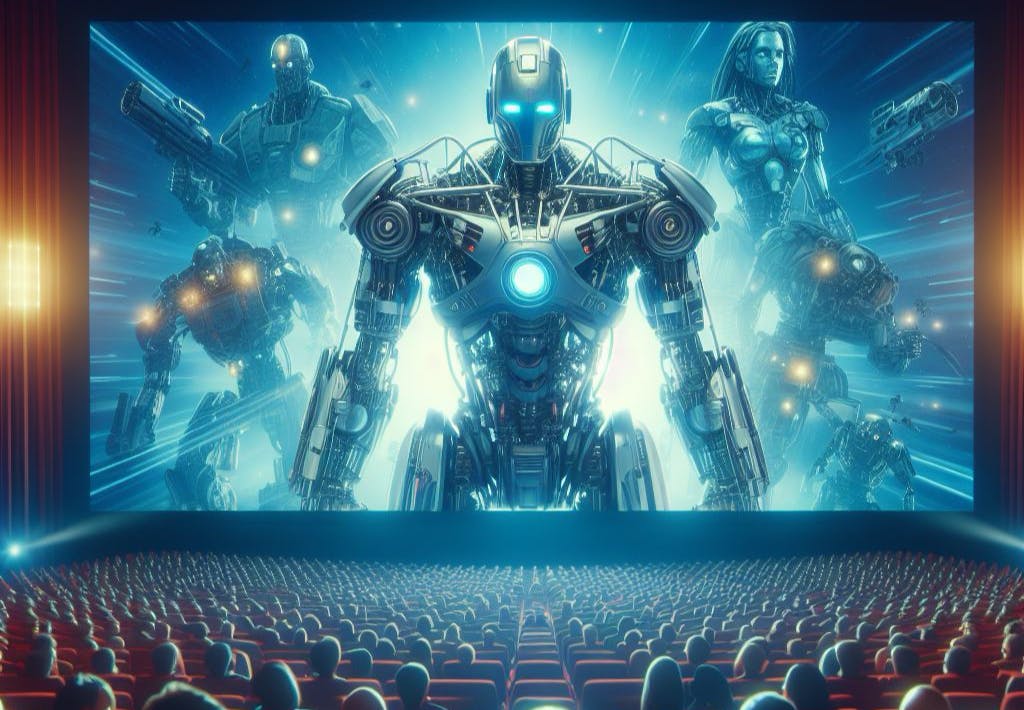
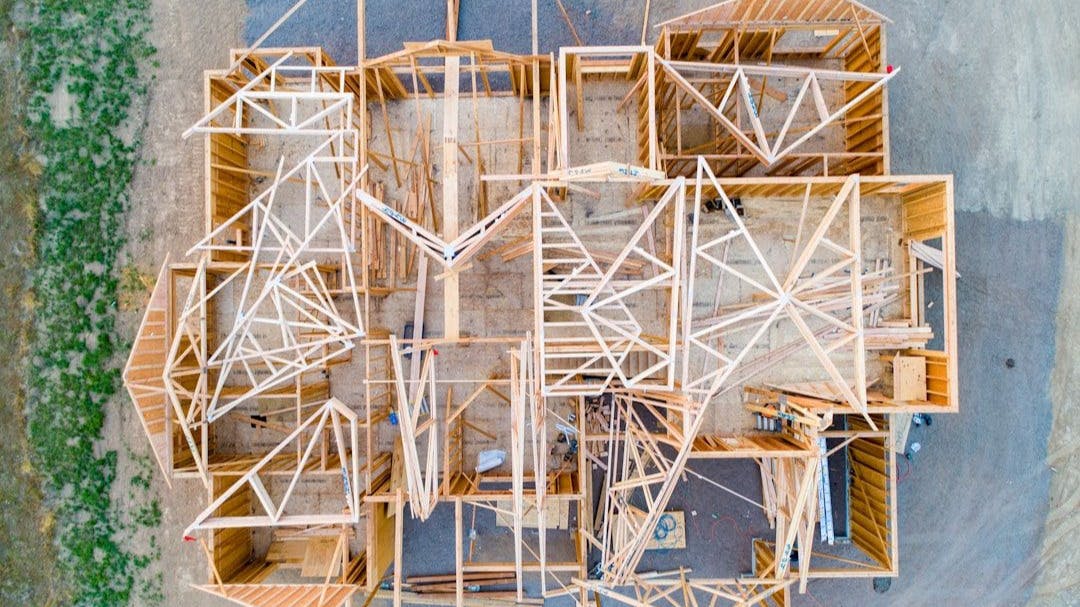
Using Scanned Mesh Data for Auto-Digitized 3D Modeling: Methodology
:::info Authors: (1) Ritesh Sharma, University Of California, Merced, USA rsharma39@ucmerced.edu; (2) Eric Bier, Palo Alto Research Center, USA bier@parc.com; (3) Lester Nelson, Palo Alto Research Center, USA lnelson@parc.com; (4) Mahabir Bhandari, Oak Ridge National Laboratory, USA bhandarims@ornl.gov; (5) Niraj Kunwar, Oak Ridge National Laboratory, USA kunwarn1@ornl.gov. ::: Table of Links Abstract and Intro Related Work Methodology Experiments Conclusion & Future work and References 3 Methodology We compute floor plans in four main steps (see Algorithm 1). First, a user captures the interior of the building as a triangle mesh using an augmented reality headset. The mesh is oriented to align with primary axes, and the building is divided into stories. Floors and ceilings are removed, and flat walls are detected if desired. Finally, one of two floor plan styles is generated by slicing and projecting the resulting 3D model. Next we describe these steps in detail. Data collection Indoor environments can be captured in various formats using different devices. We use a Microsoft HoloLens 2 headset to capture triangle mesh data, annotating the mesh using voice commands. Capturing the triangle mesh The HoloLens provides hardware and software to create a 3D representation of the indoor environment using triangles, as shown in Figure 1-left. The headset overlays the triangles on the user's view of the building interior. Although the headset captures most of the walls, floors, and ceilings, data may be missing from some regions, as in the figure. Annotating the mesh To capture object positions such as sensors, thermostats, windows, and doors, we developed an augmented reality (AR) user interface. This interface uses eye gaze detection and voice commands to enable users to place synthetic objects at desired locations, as shown in Figure 1-right where a synthetic sensor object is added to the immersive environment, superimposed on a physical sensor. 3.1 Mesh orientation After the annotated triangle mesh is captured, geometric processing is performed. Initially, the mesh's orientation is based on the user's starting position and gaze direction. To generate a floor plan, we must determine the floor's position and facing direction. The AR headset provides a rough estimation of gravity direction, but additional computation improves precision. Orienting the floor To determine the mesh orientation, we tested two methods: (1) compute the shortest edges of the mesh bounding box, and (2) cluster the facing directions of mesh triangles using spherical k-means. Method (1) works for buildings with constant altitude and large floor area, but it fails on others, so we mainly use Method (2), described in Algorithm 2. Algorithm 2 applies to a broad range of meshes, including multi-story buildings with vertical dominance. It uses the surface normal vector of each triangle ∆ in the mesh M and filters out triangles deviating significantly from the positive y direction, preserving those likely to represent the floor (∆ ′). We use a spherical coordinates k-means algorithm with k = 1 to find the dominant direction gm of these triangles. We discard triangles that are more han an angle ϕ from the dominant direction and repeat the k-means algorithm until ϕmin is reached (e.g., start with ϕ = 30 degrees and end with ϕmin = 3). This gives an estimate of the true gravity direction gt. To orient the mesh, we compute the angle θ between gt and the negative yaxis and determine the rotation axis Y by taking their cross product. We rotate the mesh by θ around the Y axis, ensuring a horizontal floor. Further details on this method for floor orientation are in Algorithm 2. Figure 2 shows a model where the floor is not level, but tilts down from near to far and from right to left. After Algorithm 2, the floor is horizontal. Finding the height of the floor After orienting the mesh to have a horizontal floor, we find the altitude of the floor in the y direction: we take the centroid of each mesh triangle whose facing direction is within a small angle of the positive y axis. We create a histogram of the y coordinates of these centroids, with each bucket representing a vertical range, such as 2 inches. We consider adjacent pairs of buckets and look for the pair with the highest number of points, such as (0, 1), (1, 2), etc. For a single-story building, we search for two large bucket pairs representing the floor (near the bottom) and the ceiling (near the top). If the building has sunken floors or raised ceilings, the histogram will show spikes at similar but not identical altitudes. To ensure that we locate true ceilings and floors, we search for a gap of several feet (such as the expected floor-to-ceiling height of a room) between the low and high histogram spikes. The spikes below this gap are probably floors, and those above are probably ceilings. To generate the floor plan, we choose the highest of the floor levels and the lowest of the ceiling levels as the computed floor and ceiling levels, respectively. Pairing the buckets rather than taking them individually ensures that we do not overlook spikes in the histogram if the mesh triangles are distributed evenly across two adjacent buckets. Rotate mesh and associated annotations Our next goal is to align the mesh model's primary wall directions with the axes of Euclidean coordinates. One optional step is to eliminate mesh triangles whose surface normals are within a small angle from the positive or negative y directions, as these are probably ceiling or floor triangles. This step is not mandatory, but decreases the number of triangles to be processed. Additionally, we eliminate all triangles below the computed floor altitude and all above the computed ceiling altitude. We then examine the surface normals of the remaining triangles. We express each normal in spherical coordinates and use spherical k-means clustering to identify the dominant wall directions. Assuming the building has mainly perpendicular walls, there will be four primary wall directions, so we can set k = 4 for k-means clustering. If the model still has floor and ceiling triangles, we can set k = 6 to account for the two additional primary directions. Figure 3-left illustrates a heat map of surface normal directions in spherical coordinates from an office building mesh. Figure 3-left contains many light blue rectangles that are far from any cluster center (e.g., far from the buckets that are red, orange, and white). These represent triangles whose facing directions do not line up with any of the primary walls, floors, or ceilings. Such triangles exist for two reasons: (1) Building interiors contain many objects that are not walls, floors, or ceilings, such as furniture, documents, office equipment, artwork, etc. These objects may be placed at any angle. (2) The AR headset generates triangles that bridge across multiple surfaces (e.g., that touch multiple walls) and hence point in an intermediate direction. To compensate, we use a modified version of spherical coordinates k-means clustering that ignores triangle directions that are outliers as follows: After computing spherical k-means in the usual way, we look for all triangles in each cluster whose facing direction is more than a threshold θ1 from the cluster center. We discard all such triangles. Then we run k-means again, computing updated cluster centers. Then we discard all triangles that are more than θ2 from each cluster center where θ2 < θ1. We repeat this process several times until we achieve the desired accuracy. For example, in our current implementation, we use this sequence of angles θi in degrees: [50, 40, 30, 20, 10, 5, 3]. Once our modified k-means algorithm completes, we have 4 (or 6) cluster centers. Figure 3-right shows sample results for k = 6. Once the primary wall directions are computed, we pick the cluster with the largest number of triangles, take its direction (cluster center), project that direction onto the x−z plane, and call it θwall. We rotate the mesh by the angle between θwall and the x axis. Now the primary walls will be pointing along the x axis. Figure 4-left shows a building that is not aligned with the axes. Figure 4- right shows the same building after wall rotation. Adding in the x axis (in red) and z axis (in blue), we see that the walls are now well-aligned with the axes. Dividing a mesh into separate levels The HoloLens can digitize multi-story buildings. Given a multi-story model, we can compute a floor plan for each story. The process is similar to the one used in 3.1 to find the height of the floor. First, our system computes a histogram, as shown in figure 5 and segments the building into multiple levels, as shown in figure 5-middle and right. 3.2 Floor plan computation Our floor plan computation depends on the type of floor plan desired and whether the mesh is oriented with respect to the global axes. If we desire a pen-and-ink style floor plan and the mesh is oriented, we can simply pass the mesh M to the ComputeAndSuperimposeSlices() function, as in line 14 of Algorithm 3.2. However, if the mesh is not properly oriented, we align it with the global axes before computing the floor plan. If a drafting-style floor plan is desired, we utilize lines 2-13 of Algorithm 3.2 to compute flat walls. Computing flat walls To generate a drafting-style floor plan, we compute flat walls and separate them from other building contents using these steps: DBSCAN For each wall direction, we perform a modified DBSCAN algorithm: We compute the centroid C of each triangle ∆i . For each centroid point Ci during DBSCAN, we count the number of other centroid points that are near enough to be considered neighbors. However, instead of looking for neighbors in a sphere around each point as for traditional DBSCAN in 3D, we look for neighbors in a rectangular block of length l, width w and height h centered on the point. This block is tall enough to reach from floor to ceiling in the y direction, a little less wide than a door in the direction parallel to the proposed wall (e.g., 1.5 feet), and a few inches in the wall direction (to allow for walls that deviate slightly from being perfectly flat). Relying on the National Building Code, the wall's minimum height is set at 8 feet, with a thickness of 8 inches. After DBSCAN, the mesh triangles are grouped into wall segments W S. Filtering We discard wall segments that are not good candidates, such as walls that are too small, that aren't near the floor, or that aren't near the ceiling. Plane fitting For each wall segment, we find a plane that has the same facing direction as the wall direction and that is a good fit to the triangle centroids in that wall segment. Given that the points are tightly collected in this direction, simply having the plane go through any centroid works surprisingly well. However, it is also possible to choose a point more carefully, such as by finding a point at a median position in the wall direction. Rectangle construction For each remaining wall segment, we construct rectangles R that lie in the fitted plane and are as wide as the wall segment triangles in width and as tall as the wall segment triangles in height. Mesh replacement For floor plan construction, we discard the original mesh triangles and replace them with the new planar wall rectangles to serve as a de-cluttered mesh. If the subsequent steps use libraries that expect a triangle mesh, we use two adjacent right triangles in place of each rectangle. for each i such that 0 ≤ i ≤ n. For each yi , we compute the intersection of the mesh with the plane y = yi . We end up with a stack of slices (see Figure 7). We can use the same method to produce a drafting-style floor plan. In this case, we begin with the flat wall model instead of the full mesh. This model has fewer details to capture by slicing at multiple altitudes, so we may choose to slice at a single intermediate altitude. Drawing the floor plan For either style of floor plan, we can project the slices to a plane by ignoring the y coordinates of the resulting line segments and plotting the resulting (x, z) coordinates as a two-dimensional image. We have also found it informative and aesthetically pleasing to draw the lines of each slice in a partially-transparent color, so that features that occur at multiple altitudes appear darker than features that occur only at a single altitude. As an example, Figure 8-left shows a mesh gathered from a commercial building. Figure 8-center shows the result of our DBSCAN on that data. Figure 8-right shows the flat walls that result after mesh replacement. Figure 9-right shows the drafting-style floor plan that results from slicing the flat walls. Figure 9-left shows the pen-and-ink floor plan made by slicing the oriented mesh at multiple altitudes. Drawing synthetic objects Because our data comes from an AR headset, we can add synthetic objects to mark the positions of objects in a room, such as sensors and windows. We can display these objects in our 3D models and floor plans. For the steps of mesh processing described above, we note the geometric transformations applied to the mesh and apply the same transformations to the synthetic objects, which then appear in the correct places in the 3D views and in the floor plans. For example, the black objects in Figure 8-left represent the objects placed by the user to show the positions of sensors and windows. Likewise, the red objects in the floor plan of Figure 9-left are those same objects, projected onto the same plane as the mesh slices. :::info This paper is available on arxiv under CC BY-NC-ND 4.0 DEED license. :::
Using Scanned Mesh Data for Auto-Digitized 3D Modeling:...
:::info
Authors:
(1) Ritesh Sharma, University Of California, Merced, USA rsharma39@ucmerced.edu;
(2)...
Source: Hacker Noon
Backstory Of The World’s Second CISO

This week in cybersecurity from the editors at Cybercrime Magazine – Listen to the Cybercrime Magazine Podcast Interview Sausalito, Calif. – May 8, 2024 The chief information security officer (CISO) role dates back to 1994, when financial services giant Citigroup (then Citicorp, ranked 17th on the The post Backstory Of The World’s Second CISO appeared first on Cybercrime Magazine.

Backstory Of The World’s Second CISO
This week in cybersecurity from the editors at Cybercrime Magazine – Listen to...
Source: Cybersecurity Research
Social Engineering Attacks: One of the Biggest and Quietest Threats to Your Business
While hackers don't differentiate between the size of their victims, certain attacks, like social engineering attacks, are most common in SMBs and SMEs. This blog specifically addresses the unique challenges and threats you may face as a small and medium-sized business or enterprise (SMB/SME) owner. Not for nothing, social engineering attacks are termed – unseen perils, silent threats to your small business and enterprise. Social Engineering Attacks: The Stats and The Reports Picture this: 📌 Per the report by Barracuda, small businesses witness 350% more social engineering attacks than larger enterprises. 📌 More than 30% of small businesses in the US have weak points that threat actors can exploit. 📌 Per the recent Verizon Data Breach Investigation Report, social engineering attacks, system intrusion, and privilege misuse incidents account for 92% of breaches in small businesses. It is essential to understand what a social engineering attack is and how it impacts your small business to understand how it affects you. What Is Social Engineering? As Cisco puts it, social engineering is not a cyberattack at its heart. It is the art of persuasion and human psychology. The modus operandi here is to target the minds of the victims like conmen and gain their trust. With the victims' trust gained, the attackers go in for the kill by encouraging them to 📍Divulge personal information 📍Click on malicious web links 📍Open malware-infected attachments So, what is Social Engineering? Let's look at the definition. Social Engineering: The Definition Any manipulation technique that exploits human errors to gain personal information, access, or valuables is a social engineering attack. In technical terms, social engineering is the psychological manipulation of people into divulging confidential information or performing unsafe actions. In layman's terms, social engineering is an assault on your emotions and feelings to extract sensitive and personal information for malicious purposes. In the world of cybercrime, scams related to human hacking are on the rise. These scams target unsuspecting users, playing tricks with their minds and luring them into revealing sensitive data and confidential information. Social engineering attacks can happen 👉 Online 👉 In-person 👉 Other interactions How Does Social Engineering Work? Social engineering works in four steps. But essentially, it works on your cognitive biases, where a threat actor impersonates either an authoritative person or a trustworthy individual and cons you into trusting them. They work in four steps. Preparation This is where a threat actor collects information about your business, and this may include your business emails, messaging apps, and other sensitive information related to your business. Infiltration This is where a bad actor will approach you or your employees. They usually imitate a reliable resource and use the previously gathered information to validate themselves. Exploitation Here, a threat actor will use persuasion tricks to obtain more sensitive information from your employees or even you. The threat actor plays on the human mind and tricks you into revealing some sensitive information. Disengagement Once an attacker has the information they sought, they will cut off all ties with you, deploy malware in your office network, and disappear in thin air. Why are SMBs and SMEs Prime Targets? Whether you have a small business or a small enterprise, you are at risk of social engineering attacks. Here are the prime reasons threat actors love your small business or your small enterprise. 📍Lack of resources is one of the primary reasons threat actors target your small business or small enterprise. 📍Trusting Culture of SMBs/SMEs is an important reason for threat actors to love small businesses and enterprises. 📍Your overworked and overburdened employees who juggle multiple responsibilities are the prime targets of threat actors. So, how do you counter these attacks on your business? Top Ways To Protect Your Small Business From Social Engineering Social Engineering attacks can be devastating for your small business, and your business may suffer: 📍Significant financial losses 📍Downtime 📍Reputational damage 📍Loss of Stakeholder and customers' trust You can counter social engineering attacks on your small business with these methods. 📌Train your employees to recognize 📍Phishing emails 📍Suspicious phone calls 📍Unsolicited requests for sensitive data 📌 Verify each email for sender addresses and the legitimacy of the data requests. 📌 Deploy two-factor authentication or multi-factor authentication on all your accounts for better security. 📌 Data encryption is your ally; embrace it with both hands. Encrypt your data at rest and in transition. When you follow these steps, you can ensure that your small business is protected from social engineering attacks. While you are at it, here are some common scams to watch out for. Common Scams to Watch Out For While practicing the four ways you can mitigate the threat of social engineering attacks, keeping an eye on some of the most common scams prevalent is essential. 📌 Phishing 📌 Tech Support Scams 📌 Pretexting 📌 Baiting 📌 Malware 📌 CEO Fraud Each of these scams is also an individual scam, but they can be deployed for sophisticated social engineering attacks. The best method to prevent social engineering attacks is to create awareness about the various tactics used by threat actors. Final Words Social engineering is becoming dangerous because attacks have become sophisticated with tech evolution. Threat actors indulging in social engineering are master con artists who know how to trick you into revealing sensitive information by invoking extreme emotions in you and your employees. So, the best way to protect your small business from social engineering is to educate your employees.
Social Engineering Attacks: One of the Biggest and...
While hackers don't differentiate between the size of their victims, certain...
Source: Hacker Noon
LiteSpeed Cache WordPress plugin actively exploited in the wild

Threat actors are exploiting a high-severity vulnerability in the LiteSpeed Cache plugin for WordPress to take over web sites. WPScan researchers reported that threat actors are exploiting a high-severity vulnerability in LiteSpeed Cache plugin for WordPress. LiteSpeed Cache for WordPress (LSCWP) is an all-in-one site acceleration plugin, featuring an exclusive server-level cache and a collection […]

LiteSpeed Cache WordPress plugin actively exploited...
Threat actors are exploiting a high-severity vulnerability in the LiteSpeed Cache...
Source: Security Affairs
MITRE Shares Details on Nation-State Hackers’ Intrusion into Research Network
%20(1)%20(1).webp)
The MITRE Corporation, a not-for-profit organization that operates research and development centers for the U.S. government, has disclosed that sophisticated nation-state hackers recently compromised one of its internal research and development networks. The intrusion, believed to have been carried out by a Chinese threat actor group known as UNC5221, exploited two zero-day vulnerabilities in Ivanti […] The post MITRE Shares Details on Nation-State Hackers’ Intrusion into Research Network appeared first on Cyber Security News.
development centers Hackers Intrusion MITRE Reveals MITRE Shares Network Attack ROOTROT Webshell
%20(1)%20(1).webp)
MITRE Shares Details on Nation-State Hackers’...
The MITRE Corporation, a not-for-profit organization that operates research and...
Source: Latest Hacker and Security News
Is It Game Over for Cheaters? Using Blockchain Technology to Eliminate Unwanted Gaming Behavior

When in-game cheating becomes the norm, does the gaming industry have a major problem on its hands? A global study of the gaming industry would say yes. It was found that 77% of online gamers are likely to stop playing a multiplayer game online if they think other players are cheating, and 48% of online gamers are likely to buy less in-game content. Add in the accrued value of digital assets as a key feature of blockchain gaming, and developers have an obligation to tackle this problem head-on. An attractiveness to bending the rules is not something limited to the world of online gaming; it is rife in all parts of society. However, as social psychologist Corey Butler points out ‘anonymity (playing with strangers or online) and opportunity can tip the scales toward greater cheating. When strong incentives like money or grades are on the line, otherwise honest people might be tempted to cheat. If somebody with a competitive nature is presented with the opportunity to easily outperform the other at a task, then it's safe to say that many will bite the bullet and risk the reward for the easy win—factor in the monetary value of rewards in Web3 gaming, and this desire to win increases significantly. However, when it comes to multiplayer online games, the competition is designed around entertainment, fun, and the community. These core values of gaming make cheating a stain on the industry as a whole. Cheating is the new norm. Cheating in some of the largest games has become an economy of its own, with many platforms and YouTube channels dedicated to introducing cheating, hacks, and navigating the ways to cheat. Don't believe us, simply type fortnite cheat terms into a google search. Combating this trend is critical for maintaining the reputation of these brands. Simon Vieira, CEO of MixMob, a Solana-based gaming platform, believes the temptation to cheat is rife, but it is nothing new, “Web3 games offer enhanced incentives due to the tangible value of game coins and digital items. However, this also creates a greater temptation to cheat. That said, traditional gaming has previously addressed similar issues. For instance, real money gaming employs methods such as biotic randomness to obscure certain game aspects like matchmaking. This approach reduces predictability, thus diminishing the incentives to cheat while still maintaining a skill-based gaming environment. We apply these strategies at MixMob to ensure fairness and keep the game engaging for all players,” says Vieira. When hacking games, cheaters now have an endless stack of tools to choose from when it comes to infiltrating game mechanics with glitching and farming to using aimbots in the software and speed hacks. This problem is exacerbated in Web3 gaming as it lacks an authoritative host. “Fair play is crucial in multi-player games as it directly impacts player engagement and retention. A fair environment ensures that players feel valued and that the game remains competitive and enjoyable for everyone,” notes Vieira. Furthermore, with AI, it is easier than ever to predict patterns of player behavior and create new ways to exploit and manipulate gaming data. So, how can this problem be addressed without compromising the gaming experience? Speaking to Tashi Protocol CEO Sandeep Bhatia, it is clear that consensus will play a future role in blockchain gaming. “Dynamite as the network transport for multiplayer games can prevent certain forms of cheating like 'lag switching' or local state hacking. The benefit of having consensus on top of a peer-to-peer network layer ensures that players cannot cheat, and the architecture reduces costs.” Frustration with the publishers Publishers are tackling the issue of one player, or several players at a time, by banning them and using anti-cheat software. Just last month, Activision, a gaming giant and creator of Call of Duty, banned 27,000 accounts from the game. However, this isn't deterring new cheats coming into the sector. Tackling it from the outset in the process of the game studio is the only way to ensure that both the publishers and the gamers benefit in the long run. To restore confidence, creators of blockchain games must demonstrate trust from the outset. “Shifting from a traditional gaming infrastructure to adopt a decentralized, serverless framework will optimize the entire Web3 gaming experience and solve the issue of cheating from the ground up. Not only can we reduce the costs by eliminating the need for centralized servers, but Tashi's Dynamite ensures fair distribution and protection against common security threats,” says Bhatia. Once a player sees that a game is compromised, it ruins the fun element and may even deter them from entering the environment because of security fears. In addition, the influx of bots and other hacks has led to unfair advantages within some of the most loved games. What can blockchain game publishers do? Gaming studios must take the necessary steps to demonstrate their commitment to fair play. This is essential in the blockchain space as it continues to build trust with the traditional gaming communities. At MixMob, they leverage blockchain transparency to allow the community to participate in monitoring and reporting cheaters actively. “This community refereeing not only helps maintain fairness but also fosters a sense of responsibility and integrity among players, and it has worked great for us,” says Vieira. “Web3 game publishers must take decisive steps to limit cheating. The actions taken should vary based on the severity of the cheating incident. Potential measures include banning, suspending, or permanently removing players involved in unfair practices. Additionally, publishers can adopt proven strategies from traditional gaming, such as introducing randomness to some parts of the game to reduce predictability, which helps deter cheating,” he continues. Game developers who are keen to implement anti-cheat measures are often outplayed by hackers who have mastered the art of cheating and the avoidance of detection. Sure, developers can ban cheaters who are caught in the act or embed cheat detection software. However, this doesn't prevent cheating from occurring from the outset. The vulnerabilities have already been exploited by the time the developer has their hands on the activities. If, however, a game creator starts the development process using the Tashi Consensus Protocol, it has eliminated the act of cheating from the initial design stage. “Gamers rely on trust that game developers would have implemented the best practices to ensure cheaters are punished. That is why Tashi works to educate all its gaming partners on the novel ways blockchain solves cheating issues. We make our tech easy to use and guide all our partners who might come from the Web2 world and are new to using blockchain tech,” added Bhatia. While anti-cheat software like Riot Game's Vanguard or Activision Blizzard's Ricochet stands as the frontline defense, the second layer can utilize the transparency provided by blockchain technology to fight against bad actors. Implementing innovative approaches to game development, like the Tashi Dynamite Consensus Engine, pushes gaming to a new era of fair play and reclaims the values that true gamers want to see in the game development stage. In addition to fostering a culture of fair play, a paradigm shift is necessary in the approach to combating cheating in online gaming. By 2027, the number of users in the Online Games market is expected to amount to 1.2bn users. The projected revenue in the Online Games market worldwide is expected to reach US.97bn in 2024. Reclaiming the gaming sector for true gamers who value the entire gaming experience is crucial as blockchain games position themselves alongside some of the gaming giants. n

Is It Game Over for Cheaters? Using Blockchain Technology...
When in-game cheating becomes the norm, does the gaming industry have a major problem...
Source: Hacker Noon
Navigating the Digital Age: AI’s Crucial Role in Cybersecurity Reinforcement

Harnessing the Power of AI for Advanced Cyber Threat Intelligence and Prevention By Bryan Kissinger, Senior Vice President of Security Solutions and Chief Information Security Officer, Trace3 The digital environment […] The post Navigating the Digital Age: AI’s Crucial Role in Cybersecurity Reinforcement appeared first on Cyber Defense Magazine.

Navigating the Digital Age: AI’s Crucial Role...
Harnessing the Power of AI for Advanced Cyber Threat Intelligence and Prevention...
Source: Cyber Defense Magazine
CISA & FBI Release Urges Developers to Eliminate Directory Traversal Vulnerabilities

The Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) have issued a joint Secure by Design Alert, calling on software developers and industry executives to intensify their efforts in eliminating directory traversal vulnerabilities within their products. This move comes in response to a series of high-profile cyber-attacks that have exploited […] The post CISA & FBI Release Urges Developers to Eliminate Directory Traversal Vulnerabilities appeared first on Cyber Security News.

CISA & FBI Release Urges Developers to Eliminate...
The Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau...
Source: Latest Hacker and Security News