Search results for users unable
New TunnelVision technique can bypass the VPN encapsulation
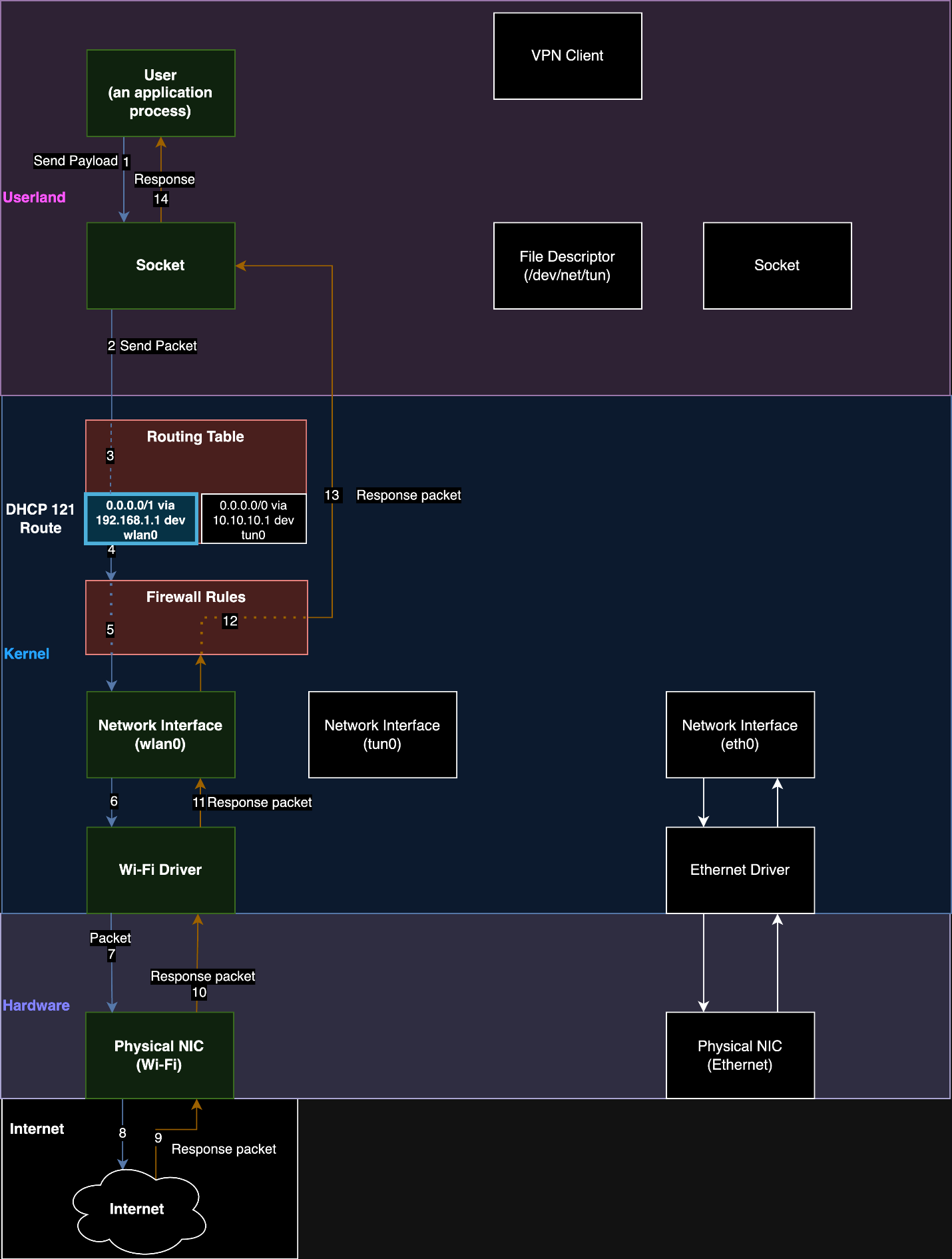
TunnelVision is a new VPN bypass technique that enables threat actors to spy on users' traffic bypassing the VPN encapsulation. Leviathan Security researchers recently identified a novel attack technique, dubbed TunnelVision, to bypass VPN encapsulation. A threat actor can use this technique to force a target user's traffic off their VPN tunnel using built-in features […]
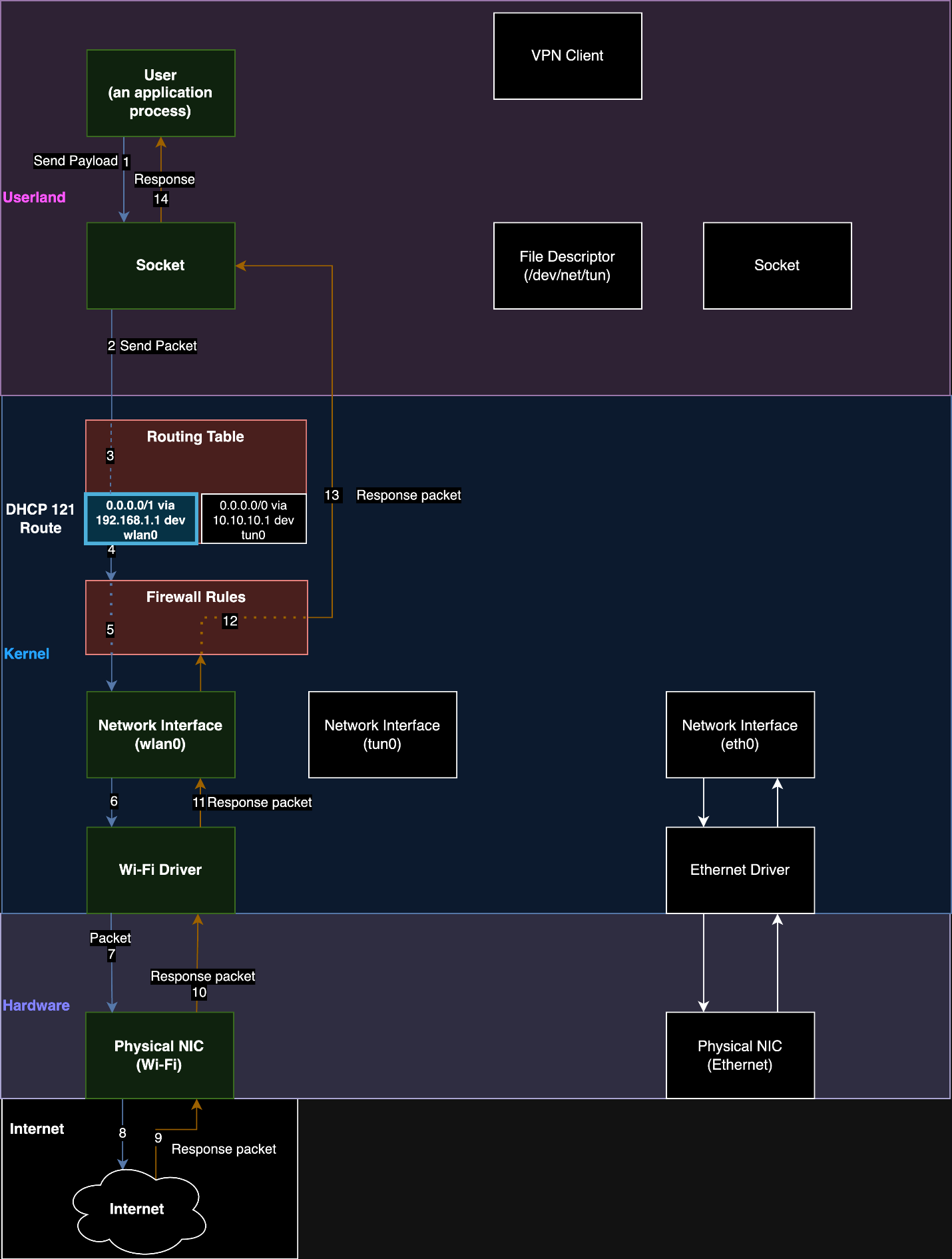
New TunnelVision technique can bypass the VPN encapsulation...
TunnelVision is a new VPN bypass technique that enables threat actors to spy on...
Source: Security Affairs
Bahamut Foundation Announces The Launch Of Three DeFi Projects And The Winners Of Bahamut Arena
Foundation has announced the Grants program to support the growing ecosystem of Bahamut and foster the expansion of decentralized projects and applications. This initiative provides multi-faceted support for a wide range of projects based on categories mainly revolving but not limited to DeFi, gaming, and NFTs. Bahamut Blockchain has already witnessed the successful results of the grants program with the latest launch of 3 DeFi projects - Lolik, Mutuari, and SilkSwap. These platforms have successfully passed all the qualification stages and, after an extensive development process, are now live on the Bahamut blockchain. The appearance of new DeFi projects will surely increase the scalability and adaptability of the native coin of Bahamut, FTN, and expand its usability and relevance. Mutuari is a lending protocol made for decentralized lending and borrowing of assets directly on Bahamut. Mutuari gives the users access to diverse crypto assets, including FTN, USTD, USDC, stFTN, and is accessible through all EVM-supporting non-custodial wallets, among them Fastex Wallet, Metamask, and WalletConnect. The project has been selected and successfully completed the task under the category of “Lending Protocol” with a prize of 60.000 FTN. Lolik is the next project that has received a grant from Bahamut Foundation. It is a liquid staking platform that supports staking on leading blockchains such as Bahamut, with other blockchains, including Ethereum and Polygon, coming soon. With Lolik, each user can earn rewards by participating in the validation processes of the blockchain directly with their Web3 wallet. And the last one is the DeFi trading platform, SilkSwapthat allows users to enjoy peer-to-peer trading and easy and fast transactions. The application stays true to a pure Web3 concept, totally eliminating any third-party interactions. n n The application process continues, accepting more and more applications. The step-by-step description of the application process and information on preferable categories and their funding are available on Bahamut.io/grants. The process is transparent and fair, keeping it real with web3. Bahamut Foundation is currently announcing the list of approved applications that will start building their projects on Bahamut through the Bahamut Arena contest and wishes them the best of luck and successful completion of their projects. Gotbit Labs Category - DEX aggregator Category Prize fund - 40,000 FTN Delivery deadline - 2 months Lost Lore Category - NFT Marketplace Category Prize fund - 40,000 FTN n Delivery deadline- 4 months Blockstars (Greedy Lottery) Category - Decentralized Game Category Prize fund - 13,000 FTN Delivery deadline - 1 month Erinaceus RNG Oracle Category - RNG Oracle Category Prize fund - 50,000 FTN Delivery deadline - 3 months Erinaceus Price Feed Oracle Category - Price Feed oracle Category Prize fund - 50,000 FTN Delivery deadline - 3 months n Additionally, the Bahamut Foundation is hosting a series of meetups at theftNFT Phygital Spaces located in Dubai, Venice, and Yerevan. These events are designed to promote community engagement by bringing together Web3 developers, newcomers, and enthusiasts. The meetups aim to foster growth and development within the global and local Web3 sector through knowledge exchange and collaboration. Moreover, a partnership with Yerevan State University has been announced to support blockchain education and community development in Armenia's growing Web3 industry. This collaboration--formalized through a memorandum of cooperation--represents a significant step towards integrating educational and research programs focused on blockchain and virtual assets, underscoring a shared commitment to promoting blockchain education and community development. About Bahamut Foundation The Switzerland-based Bahamut Foundation stays at the forefront of innovation, offering support and funding to the projects that foster advancements in the field, generate value for the blockchain ecosystem, and bring new users into the world of Web3, laying the foundations for future generations to learn and build upon. :::tip This story was distributed as a release by Btcwire under HackerNoon's Business Blogging Program. Learn more about the program here. :::
Bahamut Bahamut Arena Bahamut Foundation Category Prize DeFi Projects
Bahamut Foundation Announces The Launch Of Three...
Foundation has announced the Grants program to support the growing ecosystem of...
Source: Hacker Noon
ChainGPT Pad Launches Engines Of Fury, Enhancing Web3 Gaming Experiences For Mainstream Players
DOVER, DE, USA, May 8, 2024 —ChainGPT, the AI-powered Web3 infrastructure providing a diverse suite of tools and services, will exclusively launch the IDO of its latest launchpad project, Engines of Fury: a free-to-play top-down extraction shooter designed for Web3. Developed by talents from AAA titles, Blizzard, Activision, Ubisoft, and Unity, its top-down characteristic makes it a first within Web3's free-to-play shooter arena. Set for May 8, Engines of Fury's IDO leverages ChainGPT Pad's acceleration program, enabling the game to perfect its product systems, action plans, and roadmaps while receiving expert marketing and promotional support. As a premier decentralized fundraising and incubation platform for Web3 projects of all types, the ChainGPT Pad has been recognized as the most popular launchpad of 2023. The incubation program promotes emerging startups strategically hand-picked by ChainGPT based on their disruptive potential, transforming their ideas into viable business solutions. The program extensively assists in product development, smart contract implementation, and user engagement. Through expert mentorship and access to an extensive network of influential partners and investors, the ChainGPT Pad's incubation provides Web3 startups with the tools to navigate inevitable challenges and thrive. Engines of Fury immerses players in a dystopian world ravaged by a mutagenic virus from a meteor. Gamers navigate a perilous universe—scavenging for resources, enhancing hideouts, and upgrading gear while honing their abilities through single-player and cooperative modes. With a robust in-game economy driven by its native $FURY token, the game emphasizes a journey of survival, craftsmanship, and community. Engines of Fury's goal is to create a game that introduces mainstream players to the distinct advantages of blockchain without forcing Web3 elements into core aspects of gameplay. Making it simple for all players to jump into the game, Engines of Fury's crypto aspects serve as a bonus, not a must. The game includes classic gaming elements with an easy onboarding process for non-crypto natives, with features such as: NFT Mining and Trading: Players discover resources and forge unique NFTS to enhance their character's abilities and appearance. Gamers can trade these NFTs freely on the Engines of Fury marketplace and other compatible platforms. Play-And-Earn Mechanics: Players can earn in-game virtual currency that can potentially convert to real-world income. Earned crypto assets and NFTs remain fully under the player's ownership. Skill-Based Rewards: Top players earn $FURY tokens based on leaderboard rankings, achievements, and in-game activities. Council Crates: Special, limited-quantity NFTs will be available during the Engine of Fury NFT Presale event. Cross-Game Interoperability: Engines of Fury collaborates with exciting projects to enable asset interoperability, expanding gameplay possibilities and community engagement. With an overwhelming response, Engines of Fury attracted over 80,000 applications for its Private Alpha Test, extending the game's original playtest deadline. The enthusiasm following the private alpha test underscores the demand for high-quality Web3 gaming experiences. Engines of Fury IDO information: Token price: $.20 IDO date: May 13th Token ticker: $FURY Allocation size: 250,00 Max supply: 120,000,000 Network: Binance Smart Chain IMC (without liquidity): 6,667 IMC (with liquidity): ,376,667 Circulating supply at TGE: 6,883,333 Fully Diluted Valuation at TGE: million Vesting schedule: 15 percent TGE, 2-month cliff, 12 months linear vesting “It has been a pleasure collaborating with Engines of Fury, who brilliantly blend blockchain-based assets with a high-quality and engaging gaming experience,” says Ilan Rakhmanov, CEO and Founder of ChainGPT. “Engines of Fury exemplifies the unique and inclusive gaming experiences that resonate with a global audience. Their IDO represented an exciting opportunity for the community to support pioneering projects that reshape the gaming landscape for more than 3.3 billion players worldwide.” “With the help of ChainGPT, we've crafted a game that serves as a prime example of how gamers and developers can collaborate to build immersive experiences that rival traditional gaming structures,” says Saulius Aleksa, Co-Founder and CEO of Engines of Fury. We are grateful for the collaboration with the talented team at ChainGPT, whose expertise and invaluable guidance have been instrumental throughout the development of our game.” About ChainGPT: ChainGPT is the leading provider of AI-powered infrastructure for crypto, blockchain, and Web3. From a next-generation IDO launchpad and incubator to automated smart contract generation and auditing, as well as an advanced Web3 AI chatbot to AI-powered news aggregation, an AI training assistant, cross-chain swap, and an NFT generator, ChainGPT is a sophisticated, end-to-end solution for AI Web3 infrastructure. By integrating large language models (LLM) with blockchain, the company builds advanced, accessible, and user-friendly tools for all users. Further solidifying its position at the forefront of technological innovation, ChainGPT has established strategic partnerships and received recognition from notable tech leaders such as Google, Nvidia, BNBChain, and Chainlink. ChainGPT aims to advance the use of AI within the blockchain space. For more information, visit:
ChainGPT Pad Launches Engines Of Fury, Enhancing Web3...
DOVER, DE, USA, May 8, 2024 —ChainGPT, the AI-powered Web3 infrastructure providing...
Source: Hacker Noon
Leading Asian Crypto Info Provider CoinNess launches English Live Feed With Free API Offer

SEOUL, South Korea, May 7, 2024—CoinNess, one of the largest cryptocurrency investment information providers in Asia, today launched its English service with a Live Feed feature for global audiences. CoinNess's Live Feed service provides real-time updates for investors in the blockchain and cryptocurrency industry. Founded in 2018, CoinNess has quickly established a strong presence, amassing an extensive user base of over 1 million across Asia, extending beyond South Korea. Renowned for its rapid distribution of the latest cryptocurrency updates, CoinNess aims to deliver breaking news within five minutes of new industry developments, ensuring continuous, around-the-clock coverage. Since the platform's launch, the Live Feed feature has generated over 200,000 news briefs for investors. CoinNess is also the largest provider of cryptocurrency investment information for institutions in South Korea. Some 40 crypto-related platforms have integrated CoinNess's Live Feed API into their services. n In 2023, CoinNess gained significant attention when it was selected by Naver, South Korea's largest search engine, to be the exclusive provider of live cryptocurrency updates as the internet giant made its first foray into displaying this type of content. In its latest development, CoinNess has forged a partnership with Yonhap Infomax, the financial news provider of the national news agency Yonhap News, to exclusively provide a live crypto feed. On May 7, CoinNess introduced the English Live Feed service for retail investors, along with a business-to-business (B2B) application programming interface (API) that its partners can implement into their services. In addition to Live Feed, CoinNess offers a comprehensive suite of information offerings related to crypto investment, including Asian market analysis, market data, on-chain data, and personalized curation of social media posts. Regarding the company's latest service introduction, CoinNess CEO Kim Jungho said, "Renowned Asian crypto exchanges, legacy media outlets, wallet providers, and online communities have implemented our Live Feed API to offer a fuller user experience for their customers." In preparation for the English Live Feed launch, CoinNess hired over ten professional content writers with extensive backgrounds in the crypto sector. This acquisition of new talent has raised the company's workforce to 50, covering both its Korean and English services. CoinNess boasts a seasoned content team and its own advanced algorithm that monitors and collects real-time data from a wide range of sources, including global media outlets, government agencies, social media platforms, crypto exchanges, and on-chain data providers. This comprehensive approach enables the CoinNess team to publish news briefs within five minutes of an issue breaking out. The platforms that have partnered with CoinNess recognize the value that the timely delivery of professional, concisely-written crypto sector news briefs brings to their users. CEO Kim expressed confidence in the new service, saying, “Our crypto Live Feed service is now accessible to institutional investors, including South Korean brokerage firms, through a terminal. This marks the first time in the world such an integration has been offered, demonstrating our service's content quality.” Lastly, in celebration of its English Live Feed service launch, CoinNess has decided to provide its Live Feed API to partners free of charge for a limited time. If you would like to avail of this value addition for the benefit of your enterprise, don't hesitate to reach out to the CoinNess business team today at business@coinness.live. :::tip This story was distributed as a release by Btcwire under HackerNoon's Business Blogging Program. Learn more about the program here. :::

Leading Asian Crypto Info Provider CoinNess launches...
SEOUL, South Korea, May 7, 2024—CoinNess, one of the largest cryptocurrency investment...
Source: Hacker Noon
Using Scanned Mesh Data for Auto-Digitized 3D Modeling: Methodology
:::info Authors: (1) Ritesh Sharma, University Of California, Merced, USA rsharma39@ucmerced.edu; (2) Eric Bier, Palo Alto Research Center, USA bier@parc.com; (3) Lester Nelson, Palo Alto Research Center, USA lnelson@parc.com; (4) Mahabir Bhandari, Oak Ridge National Laboratory, USA bhandarims@ornl.gov; (5) Niraj Kunwar, Oak Ridge National Laboratory, USA kunwarn1@ornl.gov. ::: Table of Links Abstract and Intro Related Work Methodology Experiments Conclusion & Future work and References 3 Methodology We compute floor plans in four main steps (see Algorithm 1). First, a user captures the interior of the building as a triangle mesh using an augmented reality headset. The mesh is oriented to align with primary axes, and the building is divided into stories. Floors and ceilings are removed, and flat walls are detected if desired. Finally, one of two floor plan styles is generated by slicing and projecting the resulting 3D model. Next we describe these steps in detail. Data collection Indoor environments can be captured in various formats using different devices. We use a Microsoft HoloLens 2 headset to capture triangle mesh data, annotating the mesh using voice commands. Capturing the triangle mesh The HoloLens provides hardware and software to create a 3D representation of the indoor environment using triangles, as shown in Figure 1-left. The headset overlays the triangles on the user's view of the building interior. Although the headset captures most of the walls, floors, and ceilings, data may be missing from some regions, as in the figure. Annotating the mesh To capture object positions such as sensors, thermostats, windows, and doors, we developed an augmented reality (AR) user interface. This interface uses eye gaze detection and voice commands to enable users to place synthetic objects at desired locations, as shown in Figure 1-right where a synthetic sensor object is added to the immersive environment, superimposed on a physical sensor. 3.1 Mesh orientation After the annotated triangle mesh is captured, geometric processing is performed. Initially, the mesh's orientation is based on the user's starting position and gaze direction. To generate a floor plan, we must determine the floor's position and facing direction. The AR headset provides a rough estimation of gravity direction, but additional computation improves precision. Orienting the floor To determine the mesh orientation, we tested two methods: (1) compute the shortest edges of the mesh bounding box, and (2) cluster the facing directions of mesh triangles using spherical k-means. Method (1) works for buildings with constant altitude and large floor area, but it fails on others, so we mainly use Method (2), described in Algorithm 2. Algorithm 2 applies to a broad range of meshes, including multi-story buildings with vertical dominance. It uses the surface normal vector of each triangle ∆ in the mesh M and filters out triangles deviating significantly from the positive y direction, preserving those likely to represent the floor (∆ ′). We use a spherical coordinates k-means algorithm with k = 1 to find the dominant direction gm of these triangles. We discard triangles that are more han an angle ϕ from the dominant direction and repeat the k-means algorithm until ϕmin is reached (e.g., start with ϕ = 30 degrees and end with ϕmin = 3). This gives an estimate of the true gravity direction gt. To orient the mesh, we compute the angle θ between gt and the negative yaxis and determine the rotation axis Y by taking their cross product. We rotate the mesh by θ around the Y axis, ensuring a horizontal floor. Further details on this method for floor orientation are in Algorithm 2. Figure 2 shows a model where the floor is not level, but tilts down from near to far and from right to left. After Algorithm 2, the floor is horizontal. Finding the height of the floor After orienting the mesh to have a horizontal floor, we find the altitude of the floor in the y direction: we take the centroid of each mesh triangle whose facing direction is within a small angle of the positive y axis. We create a histogram of the y coordinates of these centroids, with each bucket representing a vertical range, such as 2 inches. We consider adjacent pairs of buckets and look for the pair with the highest number of points, such as (0, 1), (1, 2), etc. For a single-story building, we search for two large bucket pairs representing the floor (near the bottom) and the ceiling (near the top). If the building has sunken floors or raised ceilings, the histogram will show spikes at similar but not identical altitudes. To ensure that we locate true ceilings and floors, we search for a gap of several feet (such as the expected floor-to-ceiling height of a room) between the low and high histogram spikes. The spikes below this gap are probably floors, and those above are probably ceilings. To generate the floor plan, we choose the highest of the floor levels and the lowest of the ceiling levels as the computed floor and ceiling levels, respectively. Pairing the buckets rather than taking them individually ensures that we do not overlook spikes in the histogram if the mesh triangles are distributed evenly across two adjacent buckets. Rotate mesh and associated annotations Our next goal is to align the mesh model's primary wall directions with the axes of Euclidean coordinates. One optional step is to eliminate mesh triangles whose surface normals are within a small angle from the positive or negative y directions, as these are probably ceiling or floor triangles. This step is not mandatory, but decreases the number of triangles to be processed. Additionally, we eliminate all triangles below the computed floor altitude and all above the computed ceiling altitude. We then examine the surface normals of the remaining triangles. We express each normal in spherical coordinates and use spherical k-means clustering to identify the dominant wall directions. Assuming the building has mainly perpendicular walls, there will be four primary wall directions, so we can set k = 4 for k-means clustering. If the model still has floor and ceiling triangles, we can set k = 6 to account for the two additional primary directions. Figure 3-left illustrates a heat map of surface normal directions in spherical coordinates from an office building mesh. Figure 3-left contains many light blue rectangles that are far from any cluster center (e.g., far from the buckets that are red, orange, and white). These represent triangles whose facing directions do not line up with any of the primary walls, floors, or ceilings. Such triangles exist for two reasons: (1) Building interiors contain many objects that are not walls, floors, or ceilings, such as furniture, documents, office equipment, artwork, etc. These objects may be placed at any angle. (2) The AR headset generates triangles that bridge across multiple surfaces (e.g., that touch multiple walls) and hence point in an intermediate direction. To compensate, we use a modified version of spherical coordinates k-means clustering that ignores triangle directions that are outliers as follows: After computing spherical k-means in the usual way, we look for all triangles in each cluster whose facing direction is more than a threshold θ1 from the cluster center. We discard all such triangles. Then we run k-means again, computing updated cluster centers. Then we discard all triangles that are more than θ2 from each cluster center where θ2 < θ1. We repeat this process several times until we achieve the desired accuracy. For example, in our current implementation, we use this sequence of angles θi in degrees: [50, 40, 30, 20, 10, 5, 3]. Once our modified k-means algorithm completes, we have 4 (or 6) cluster centers. Figure 3-right shows sample results for k = 6. Once the primary wall directions are computed, we pick the cluster with the largest number of triangles, take its direction (cluster center), project that direction onto the x−z plane, and call it θwall. We rotate the mesh by the angle between θwall and the x axis. Now the primary walls will be pointing along the x axis. Figure 4-left shows a building that is not aligned with the axes. Figure 4- right shows the same building after wall rotation. Adding in the x axis (in red) and z axis (in blue), we see that the walls are now well-aligned with the axes. Dividing a mesh into separate levels The HoloLens can digitize multi-story buildings. Given a multi-story model, we can compute a floor plan for each story. The process is similar to the one used in 3.1 to find the height of the floor. First, our system computes a histogram, as shown in figure 5 and segments the building into multiple levels, as shown in figure 5-middle and right. 3.2 Floor plan computation Our floor plan computation depends on the type of floor plan desired and whether the mesh is oriented with respect to the global axes. If we desire a pen-and-ink style floor plan and the mesh is oriented, we can simply pass the mesh M to the ComputeAndSuperimposeSlices() function, as in line 14 of Algorithm 3.2. However, if the mesh is not properly oriented, we align it with the global axes before computing the floor plan. If a drafting-style floor plan is desired, we utilize lines 2-13 of Algorithm 3.2 to compute flat walls. Computing flat walls To generate a drafting-style floor plan, we compute flat walls and separate them from other building contents using these steps: DBSCAN For each wall direction, we perform a modified DBSCAN algorithm: We compute the centroid C of each triangle ∆i . For each centroid point Ci during DBSCAN, we count the number of other centroid points that are near enough to be considered neighbors. However, instead of looking for neighbors in a sphere around each point as for traditional DBSCAN in 3D, we look for neighbors in a rectangular block of length l, width w and height h centered on the point. This block is tall enough to reach from floor to ceiling in the y direction, a little less wide than a door in the direction parallel to the proposed wall (e.g., 1.5 feet), and a few inches in the wall direction (to allow for walls that deviate slightly from being perfectly flat). Relying on the National Building Code, the wall's minimum height is set at 8 feet, with a thickness of 8 inches. After DBSCAN, the mesh triangles are grouped into wall segments W S. Filtering We discard wall segments that are not good candidates, such as walls that are too small, that aren't near the floor, or that aren't near the ceiling. Plane fitting For each wall segment, we find a plane that has the same facing direction as the wall direction and that is a good fit to the triangle centroids in that wall segment. Given that the points are tightly collected in this direction, simply having the plane go through any centroid works surprisingly well. However, it is also possible to choose a point more carefully, such as by finding a point at a median position in the wall direction. Rectangle construction For each remaining wall segment, we construct rectangles R that lie in the fitted plane and are as wide as the wall segment triangles in width and as tall as the wall segment triangles in height. Mesh replacement For floor plan construction, we discard the original mesh triangles and replace them with the new planar wall rectangles to serve as a de-cluttered mesh. If the subsequent steps use libraries that expect a triangle mesh, we use two adjacent right triangles in place of each rectangle. for each i such that 0 ≤ i ≤ n. For each yi , we compute the intersection of the mesh with the plane y = yi . We end up with a stack of slices (see Figure 7). We can use the same method to produce a drafting-style floor plan. In this case, we begin with the flat wall model instead of the full mesh. This model has fewer details to capture by slicing at multiple altitudes, so we may choose to slice at a single intermediate altitude. Drawing the floor plan For either style of floor plan, we can project the slices to a plane by ignoring the y coordinates of the resulting line segments and plotting the resulting (x, z) coordinates as a two-dimensional image. We have also found it informative and aesthetically pleasing to draw the lines of each slice in a partially-transparent color, so that features that occur at multiple altitudes appear darker than features that occur only at a single altitude. As an example, Figure 8-left shows a mesh gathered from a commercial building. Figure 8-center shows the result of our DBSCAN on that data. Figure 8-right shows the flat walls that result after mesh replacement. Figure 9-right shows the drafting-style floor plan that results from slicing the flat walls. Figure 9-left shows the pen-and-ink floor plan made by slicing the oriented mesh at multiple altitudes. Drawing synthetic objects Because our data comes from an AR headset, we can add synthetic objects to mark the positions of objects in a room, such as sensors and windows. We can display these objects in our 3D models and floor plans. For the steps of mesh processing described above, we note the geometric transformations applied to the mesh and apply the same transformations to the synthetic objects, which then appear in the correct places in the 3D views and in the floor plans. For example, the black objects in Figure 8-left represent the objects placed by the user to show the positions of sensors and windows. Likewise, the red objects in the floor plan of Figure 9-left are those same objects, projected onto the same plane as the mesh slices. :::info This paper is available on arxiv under CC BY-NC-ND 4.0 DEED license. :::
Using Scanned Mesh Data for Auto-Digitized 3D Modeling:...
:::info
Authors:
(1) Ritesh Sharma, University Of California, Merced, USA rsharma39@ucmerced.edu;
(2)...
Source: Hacker Noon
Using Scanned Mesh Data for Auto-Digitized 3D Modeling: Abstract and Introduction
:::info Authors: (1) Ritesh Sharma, University Of California, Merced, USA rsharma39@ucmerced.edu; (2) Eric Bier, Palo Alto Research Center, USA bier@parc.com; (3) Lester Nelson, Palo Alto Research Center, USA lnelson@parc.com; (4) Mahabir Bhandari, Oak Ridge National Laboratory, USA bhandarims@ornl.gov; (5) Niraj Kunwar, Oak Ridge National Laboratory, USA kunwarn1@ornl.gov. ::: Table of Links Abstract and Intro Related Work Methodology Experiments Conclusion & Future work and References Abstract This paper describes a novel approach for generating accurate floor plans and 3D models of building interiors using scanned mesh data. Unlike previous methods, which begin with a high resolution point cloud from a laser range-finder, our approach begins with triangle mesh data, as from a Microsoft HoloLens. It generates two types of floor plans, a "pen-and-ink" style that preserves details and a drafting-style that reduces clutter. It processes the 3D model for use in applications by aligning it with coordinate axes, annotating important objects, dividing it into stories, and removing the ceiling. Its performance is evaluated on commercial and residential buildings, with experiments to assess quality and dimensional accuracy. Our approach demonstrates promising potential for automatic digitization and orientation of scanned mesh data, enabling floor plan and 3D model generation in various applications such as navigation, interior design, furniture placement, facilities management, building construction, and HVAC design. Keywords: Clustering based methods · Floor plans · Augmented Reality· 3D Models. 1 Introduction Floor plans are useful for many applications including navigating in building interiors; remodeling; efficient placement of furniture; placement of pipes; heating, ventilation, and air conditioning (HVAC) design; and preparing an emergency evacuation plan. Depending on the application, different kinds of floor plan are appropriate. For remodeling building interiors or designing HVAC systems, users may prefer a drafting-style floor plan that focuses on planar walls and removes furniture and other clutter. For furniture placement, navigation, or evacuation planning, users may prefer a more detailed floor plan that shows the positions of furniture, cabinets, counter tops, etc. In either case, producing a floor plan can be time consuming, requiring expert skills, such as measuring distances and angles or entering data into a CAD program. Furthermore, it may need to be done more than once because a building changes when walls and furniture are moved, added, or removed. So it is valuable to be able to generate floor plans automatically with little or no training. To generate floor plans, it helps to begin with accurate data that can be collected automatically. Laser range finders, smartphones, tablets, and augmented reality (AR) headsets are some of the devices that have made it easier to collect high-resolution building data in the form of RGBD images, point clouds, and triangle meshes. In this paper, we describe a method for generating drafting style and pen-and-ink-style floor plans by leveraging incomplete and imperfect triangle mesh data. This approach efficiently generates both types of floor plans accurately, supporting a wide range of applications. Main Contribution We describe a new method for generating accurate floor plans using poorly captured triangle mesh data from the Microsoft HoloLens 2. The main contributions are: – A modified Density-Based Spatial Clustering of Applications with Noise (DBSCAN) algorithm, using blocks to capture wall height and thickness. – An orientation-based clustering method that finds walls at arbitrary angles. – The use of k-means clustering to rotate the mesh to the principal axes and to identify the floor and ceiling. – Generating two kinds of precise floor plans from incomplete mesh data. :::info This paper is available on arxiv under CC BY-NC-ND 4.0 DEED license. :::
Using Scanned Mesh Data for Auto-Digitized 3D Modeling:...
:::info
Authors:
(1) Ritesh Sharma, University Of California, Merced, USA rsharma39@ucmerced.edu;
(2)...
Source: Hacker Noon
Social Engineering Attacks: One of the Biggest and Quietest Threats to Your Business
While hackers don't differentiate between the size of their victims, certain attacks, like social engineering attacks, are most common in SMBs and SMEs. This blog specifically addresses the unique challenges and threats you may face as a small and medium-sized business or enterprise (SMB/SME) owner. Not for nothing, social engineering attacks are termed – unseen perils, silent threats to your small business and enterprise. Social Engineering Attacks: The Stats and The Reports Picture this: 📌 Per the report by Barracuda, small businesses witness 350% more social engineering attacks than larger enterprises. 📌 More than 30% of small businesses in the US have weak points that threat actors can exploit. 📌 Per the recent Verizon Data Breach Investigation Report, social engineering attacks, system intrusion, and privilege misuse incidents account for 92% of breaches in small businesses. It is essential to understand what a social engineering attack is and how it impacts your small business to understand how it affects you. What Is Social Engineering? As Cisco puts it, social engineering is not a cyberattack at its heart. It is the art of persuasion and human psychology. The modus operandi here is to target the minds of the victims like conmen and gain their trust. With the victims' trust gained, the attackers go in for the kill by encouraging them to 📍Divulge personal information 📍Click on malicious web links 📍Open malware-infected attachments So, what is Social Engineering? Let's look at the definition. Social Engineering: The Definition Any manipulation technique that exploits human errors to gain personal information, access, or valuables is a social engineering attack. In technical terms, social engineering is the psychological manipulation of people into divulging confidential information or performing unsafe actions. In layman's terms, social engineering is an assault on your emotions and feelings to extract sensitive and personal information for malicious purposes. In the world of cybercrime, scams related to human hacking are on the rise. These scams target unsuspecting users, playing tricks with their minds and luring them into revealing sensitive data and confidential information. Social engineering attacks can happen 👉 Online 👉 In-person 👉 Other interactions How Does Social Engineering Work? Social engineering works in four steps. But essentially, it works on your cognitive biases, where a threat actor impersonates either an authoritative person or a trustworthy individual and cons you into trusting them. They work in four steps. Preparation This is where a threat actor collects information about your business, and this may include your business emails, messaging apps, and other sensitive information related to your business. Infiltration This is where a bad actor will approach you or your employees. They usually imitate a reliable resource and use the previously gathered information to validate themselves. Exploitation Here, a threat actor will use persuasion tricks to obtain more sensitive information from your employees or even you. The threat actor plays on the human mind and tricks you into revealing some sensitive information. Disengagement Once an attacker has the information they sought, they will cut off all ties with you, deploy malware in your office network, and disappear in thin air. Why are SMBs and SMEs Prime Targets? Whether you have a small business or a small enterprise, you are at risk of social engineering attacks. Here are the prime reasons threat actors love your small business or your small enterprise. 📍Lack of resources is one of the primary reasons threat actors target your small business or small enterprise. 📍Trusting Culture of SMBs/SMEs is an important reason for threat actors to love small businesses and enterprises. 📍Your overworked and overburdened employees who juggle multiple responsibilities are the prime targets of threat actors. So, how do you counter these attacks on your business? Top Ways To Protect Your Small Business From Social Engineering Social Engineering attacks can be devastating for your small business, and your business may suffer: 📍Significant financial losses 📍Downtime 📍Reputational damage 📍Loss of Stakeholder and customers' trust You can counter social engineering attacks on your small business with these methods. 📌Train your employees to recognize 📍Phishing emails 📍Suspicious phone calls 📍Unsolicited requests for sensitive data 📌 Verify each email for sender addresses and the legitimacy of the data requests. 📌 Deploy two-factor authentication or multi-factor authentication on all your accounts for better security. 📌 Data encryption is your ally; embrace it with both hands. Encrypt your data at rest and in transition. When you follow these steps, you can ensure that your small business is protected from social engineering attacks. While you are at it, here are some common scams to watch out for. Common Scams to Watch Out For While practicing the four ways you can mitigate the threat of social engineering attacks, keeping an eye on some of the most common scams prevalent is essential. 📌 Phishing 📌 Tech Support Scams 📌 Pretexting 📌 Baiting 📌 Malware 📌 CEO Fraud Each of these scams is also an individual scam, but they can be deployed for sophisticated social engineering attacks. The best method to prevent social engineering attacks is to create awareness about the various tactics used by threat actors. Final Words Social engineering is becoming dangerous because attacks have become sophisticated with tech evolution. Threat actors indulging in social engineering are master con artists who know how to trick you into revealing sensitive information by invoking extreme emotions in you and your employees. So, the best way to protect your small business from social engineering is to educate your employees.
Social Engineering Attacks: One of the Biggest and...
While hackers don't differentiate between the size of their victims, certain...
Source: Hacker Noon
Demystifying DePINs and More: Bridging Real-World Infrastructure
What are DePINs? Decentralized Physical Infrastructure Networks (DePINs) are real-world infrastructures on-chain. In more depth, DePINs offer a community-driven, cost-effective means of scaling projects without relying on traditional, centralized models. They are platforms where organizations and individuals can benefit from higher levels of control over their data and products through decentralized infrastructure. As for the term "DePIN,” this gained prominence in 2023 and continues to grow in mention into 2024. Initially, Web3 was used to reference projects focused on networks (replicating Web2 internet networks, but decentralized) but has since expanded to include all crypto or blockchain work, resulting in the need for this specific terminology. DePIN 101 On a fundamental level, DePINs function as bridges between physical facilities and the blockchain ecosystem. They operate through three main components. These are physical infrastructure controlled by a provider, a middleware connection to the blockchain, and a public ledger. These connections are managed by record-keeping and offering remittances to both the provider and the user. n n The physical infrastructure could be a smart agriculture system where farmers use IoT (Internet of Things) devices such as soil moisture sensors, weather stations, and crop health monitors to gather data about their fields. The middleware would then relay this information to the blockchain. Then, based on the data provided by the middleware, the blockchain would distribute rewards to the provider and users in the form of tokens. n Additionally, for DePINs to operate effectively, four distinct parties must be involved in the network. This includes: Hardware (PRNs & DRNs): a physical component connecting networks to the real world Hardware operators (Providers): Contributors buying or lending their hardware to the given network Token: A financial incentive paid out to hardware operators based on data provided by the middleware Users: DePINs need users who are willing to use and pay for the service The Current DePIN Landscape DePIN projects operate in six core business niches: compute marketplaces, wireless coverage, wholesale data, services marketplaces, energy services, and vertical ad networks. At present, there are several existing projects emerging in all six of these business models, including Filecoin, Helium, Hivemapper, Braintrust, Entheos and Sweatcoin. Out of these six sectors, compute marketplaces are where the most potential is seen, making up the majority of the market capitalization of DePIN crypto projects. Unpacking a DePIN example As we can see from the current DePIN landscape, there are many sectors in which DePINs currently operate. One real-world example that makes sense, at its core, is a decentralized energy grid. The basis for this is that traditional energy grids are often centralized, owned, and operated by utility companies, which can lead to inefficiencies and a lack of flexibility in distribution. Contrastingly, a decentralized energy grid built on blockchain technology could enable peer-to-peer energy trading between consumers and producers. Imagine a scenario where homeowners could sell excess energy to neighbors from their solar panels. This would facilitate more efficient use of renewable energy resources and incentivize individuals and communities to invest in sustainable energy production. By leveraging blockchain and smart contracts, this DePIN could ensure transparent and secure transactions while empowering users to have more control over their energy usage and production. The Flywheel Effect The concept of the flywheel effect is crucial to understanding DePINs potential for network growth and scalability. Unlike traditional models that require massive upfront capital investments, DePINs rely on grassroots efforts and community-driven initiatives to scale. n Tokens play their part in these ecosystems by serving as an incentive for the community to contribute to the maintenance of the network. The Flywheel (above) visualizes the different steps involved in this maintenance and also helps to explain how DePIN projects can utilize the flywheel effect to catalyze their network growth. n n There are several different ways projects can increase the value of their token. For example, a stake-weighted random selection algorithm can be utilized to increase the value of a token, as providers must stake the project's token to get user deal flow. This adds an added incentive for contributors to continue building out the network. Therefore, the native token will increase in price as the network grows, resulting in more rewards for providers and a higher attraction for investors to invest. Fundamentally, this flywheel creates infrastructure networks that get stronger as they get bigger. As explained above, the flywheel effect of DePINs offers an alternative approach to traditional business models that fundamentally makes sense. However, we must consider the obstacles DePINs face in their journey to realizing their potential. The Future of DePINs By leveraging blockchain technology and tokenomics (The Flywheel Effect), DePINs are expected to disrupt existing IoT business models and enable on-chain communities to build innovative decentralized networks and applications. However, some limitations are currently holding DePINs back. There are several architectural considerations for scaling DePIN applications on-chain that need to be addressed if DePINs are going to be the bridge between decentralized technology and the real world. The most significant challenges to overcome are scalability, interoperability, security, and usability issues. The on-chain infrastructure needs to be able to handle a high volume of transactions and data throughput effectively to support the requirements of decentralized physical networks. To then communicate and exchange this data effectively, seamless interoperability with other blockchain networks and traditional systems is required. Robust security mechanisms, including encryption and authentication, are vital to safeguarding sensitive information and ensuring the integrity of DePIN networks. On top of this, DePINs must have systems in place, ensuring the security of external data feeds (oracles) used to verify real-world information and the prevention of Sybil attacks, where malicious actors create fake identities to gain undue influence within the network. A final consideration is that specialized technical knowledge is currently required to participate in a DePIN ecosystem. A more usable interface and intuitive design will be required for further adoption. n The future of DePINs relies heavily on collaboration among stakeholders and ongoing technological innovation to address these challenges and unlock their full potential.
Demystifying DePINs and More: Bridging Real-World...
What are DePINs?
Decentralized Physical Infrastructure Networks (DePINs) are real-world...
Source: Hacker Noon
Hackers without borders

HWB, for a better world in cyberspace. Hackers Without Borders is an international humanitarian association that provides emergency assistance to non-governmental institutions in the event of crises and disasters related to cyberattacks.

Hackers without borders
HWB, for a better world in cyberspace. Hackers Without Borders is an international...
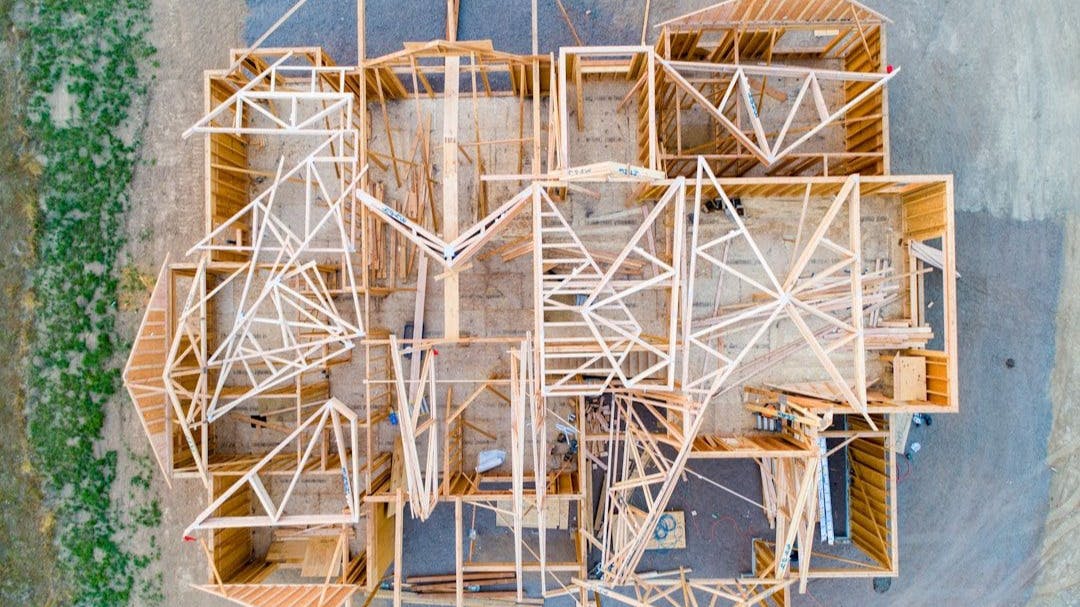
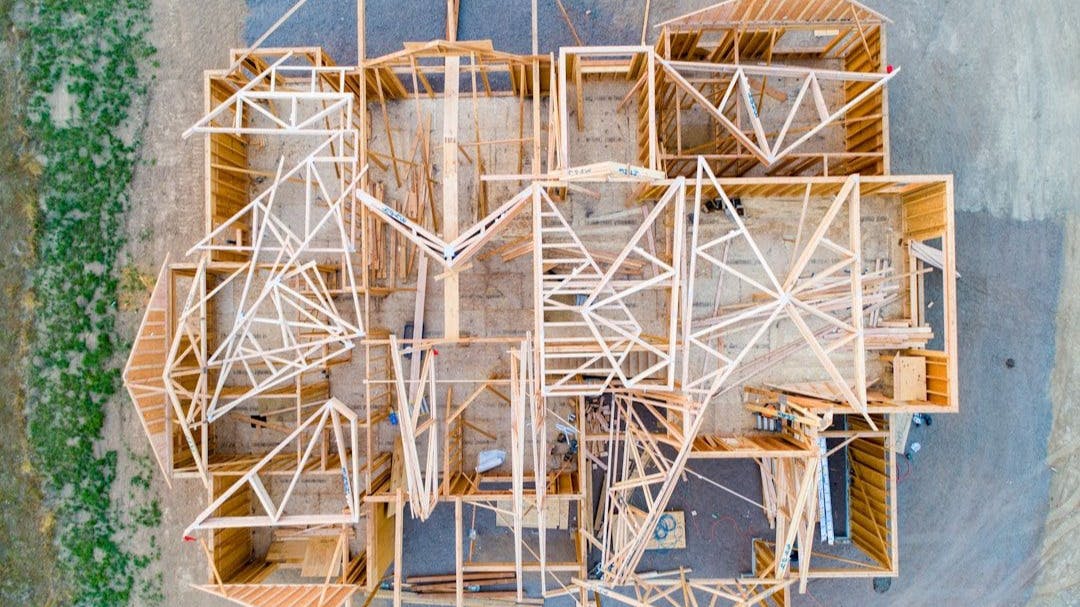
Mastering the Art of Software Development: From Developer to Craftsperson

In this blog article, we'll explore the principles of software craftsmanship, the benefits of becoming a software craftsperson, and how we can improve our skills. We'll look at a growth mindset and some resources to help us on our journey. Let's dive in! Witnessing Craftsmanship Let's say we enter a home and face this beautifully crafted staircase. Why do we even think this is beautiful? What comes to mind is the skill and work that has gone into it. The craftsperson has had to think about how to ensure that it's only connected at the top and the bottom, it can support the weight and doesn't fall under its weight, or when there are people on it, climbing up and down. There is also the craftsmanship of the handrail and the curved wall. Why does this craftsmanship strike us or cause us to take notice? Is it because we can see the care taken in creating the stairs? Or maybe we can see that a lot of skill went into it? Or perhaps it's because the knowledge of physics has been used to make it appear that it defies gravity? What Is Craftsmanship? From Collins dictionary, we can see the definition is: Craftsmanship is the quality that something has when it is beautiful and has been very carefully made. What Is Software Craftsmanship? The Manifesto for Software Craftsmanship describes it as follows: Not only working software, n but also well-crafted software. Not only responding to change, n but also steadily adding value. Not only individuals and interactions, n but also a community of professionals. Not only customer collaboration, n but also productive partnerships. If we simplify it, a software craftsperson cares about all aspects of their work. What Separates a Software Developer From a Software Craftsperson? While software developers are primarily concerned with the code they write, software craftspeople take a broader approach. They manage the code, its maintainability, deployability, and application monitoring. This results in robust applications that meet user needs and bring joy to users. Software craftspeople continually hone their skills to create better applications that perform well in production without constant supervision. Quality applications are made through thorough testing and proactive monitoring that alerts the team to potential issues. Why Choose to Embark on the Path of a Software Craftsperson? For anyone who connects with the principles of software craftsmanship — well-crafted software, steadily adding value, being part of a community, and having productive partnerships with their users — the path of software craftsperson is a good fit. It's a journey where we continually learn the craft of building software in an evolving landscape. As software craftspeople, we're not happy just throwing things out the door but instead focusing on quality and stability. We also want to build up a community of people who can create high-quality software so that we all can learn from each other and build on what others are learning. Why Did I Make the Transition to Software Craftsperson? Different people have different journeys, motivations, and experiences regarding craftsmanship. Let me tell you my story. I had worked in software development for over ten years when I joined a software craftsmanship dojo. At the start, I didn't understand the impact that the dojo would have. I thought I was only there to learn Test Driven Development (TDD). Previously, I had learned TDD by participating in code retreats. Still, I needed help incorporating the new working method into day-to-day coding outside of fixing defects or working on straightforward features. The dojo allowed me to learn hands-on each week, developing the skills that drive my development through testing. This mindset progressed to the point where I now find it hard to think about developing without using TDD. The move to software craftsmanship made sense as a path for my career since I had worked on many projects where we were fighting the storm of trying to develop the application, dealing with production issues, and managing our technical debt. This storm led me to burnout and disillusionment in the software developer career. Having an opportunity in the weekly two-hour dojo to learn new skills and have hands-on experience meant that it was two hours that I looked forward to the most in the week. Outside the dojo, I practice a daily coding exercise, use what I learned in my work, and consider new ways of doing things. This practice has led me to develop skills to quickly deploy new, well-tested applications with testing, monitoring, and scanning toolchains, improving my DORA and DASA scores. Growth Mindset Moving to become a software craftsperson will mean that we can see that there are ways that we can grow. Rather than seeing our skills as something that can't be changed, we realise we can improve incrementally over time. So, rather than having a fixed mindset where we think our skills limit our growth, we have a growth mindset. Referring to the previous post, building habits and working on getting 1% better is fundamental to creating a growth mindset. This growth mindset doesn't just stop with us; it should also include growing the people around us. Having a growth mindset is vital to building a community of software craftspeople. Benchmarking Our Skills To understand where we are with our software craftsmanship skills, we can use the DevOps Agile Skills Association (DASA) DevOps quick scan to know where we are with our skill levels. Then, we can work on improving the areas that need addressing. The quick scan looks at 12 different areas: Business Value Optimisation Business Analysis Architecture and Design Test Specification Programming Continuous Delivery Infrastructure Engineering Security, Risk, Compliance Courage Team Building DevOps Leadership Continuous Improvement Each area will receive a score from one (novice) to five (master). The report will help us understand what is required at the next level and how to improve. Methodology for Developing Quality Cloud Applications A methodology called the twelve-factor app is used to build software-as-a-service applications that can scale without significant changes to tooling, architecture, or development practices. The created app uses declarative formats for setup automation, has a clean contract with the underlying operating system, and minimizes divergence between development and production. The methodology can be applied to apps in any programming language and can use any combination of backend services. We can build the best software-as-service application possible by following the twelve factors. Getting Started on Our Journey as Software Craftspeople Understanding more about software craftsmanship can always be helpful. There is a link to further reading on the Manifesto for Software Craftsmanship. There you will see, among others: Apprenticeship Patterns: Guidance for the Aspiring Software Craftsman by Dave Hoover and Adewale Oshineye Software Craftsmanship by Pete McBreen The Pragmatic Programmer by David Thomas and Andrew Hunt A title missing from that list is: The Software Craftsman by Sandro Mancuso These titles help us further understand software craftsmanship and what we must look at in our journey. We should improve ourselves and those around us to build well-crafted software using the lessons learned. Conclusion Changing our identity from a developer to a software craftsperson leads us to build well-crafted applications. The key to the change is treating it as a journey, and as with any journey, we can take many different routes. We've talked about some of the resources that might be useful, and we can use the resources that entice us and keep us going along the journey. Transforming 1% daily will mean we will have significantly impacted how we work for a year and beyond. References Craftsmanship Definition — https://www.collinsdictionary.com/dictionary/english/craftsmanship Manifesto for Software Craftsmanship — https://manifesto.softwarecraftsmanship.org DASA Quick Scan — https://scan.devopsagileskills.org BriX Software Craftsmanship Dojo — https://swcraftsmanshipdojo.com DORA Quick Check — https://dora.dev/quickcheck The Twelve-Factor App — https://12factor.net Apprenticeship Patterns: Guidance for the Aspiring Software Craftsman by Dave Hoover and Adewale Oshineye — https://www.amazon.com/Apprenticeship-Patterns-Guidance-Aspiring-Craftsman/dp/0596518382/ Software Craftsmanship by Pete McBreen — https://www.amazon.com/Software-Craftsmanship-Imperative-Pete-McBreen/dp/0201733862 The Pragmatic Programmer by David Thomas and Andrew Hunt — https://www.amazon.com/Pragmatic-Programmer-journey-mastery-Anniversary/dp/0135957052 The Software Craftsman by Sandro Mancuso — https://www.amazon.com/Software-Craftsman-Professionalism-Pragmatism-Robert/dp/0134052501 Credits The title image is from Dreamstudio AI.
craftsmanship Software Craftsman software craftsmanship software craftsperson

Mastering the Art of Software Development: From Developer...
In this blog article, we'll explore the principles of software craftsmanship,...
Source: Hacker Noon
The TechBeat: Checklist for FinTech Product Growth: Channels, Trends, and Tools (5/8/2024)

How are you, hacker? 🪐Want to know what's trending right now?: The Techbeat by HackerNoon has got you covered with fresh content from our trending stories of the day! Set email preference here. ## Checklist for FinTech Product Growth: Channels, Trends, and Tools By @moscowgt [ 7 Min read ] What metrics should be tracked and improved upon in FinTech products during the user acquisition, activation, and retention stages? Read More. From Pre-Seed to Series A: Navigating the Key Stages of Product Development By @moscowgt [ 10 Min read ] The article showcases best practices for product development from pre-seed to Series A rounds, and describes what to pay attention to in your startup. Read More. The Power of User Feedback in Product Development By @moscowgt [ 10 Min read ] The article describes using both direct and indirect feedback methods throughout the product development lifecycle. Read More. Scaling Fintech Startups in 2024: Strategies and Challenges By @moscowgt [ 6 Min read ] The barriers for startups entering the Fintech industry are constantly increasing. Consider the strategies to gain a competitive advantage. Read More. How to Earn Million With AWS in One Year By @gianpicolonna [ 5 Min read ] Slash your AWS cloud costs by 90%! Learn 4 steps to optimize spending: challenge assumptions, tune resources, use Graviton instances, and monitor usage. Read More. How I Boosted My Productivity While Working on Multiple Projects By @alexkaul [ 4 Min read ] Freeter is a free and open-source app that helps you organize your work. It lets you switch between multiple workflows in a single place. Read More. 6 Critical Challenges of Productionizing Vector Search By @rocksetcloud [ 6 Min read ] Prepare for complexities of deploying vector search in production with insights on indexing, metadata filtering, query language, and vector lifecycle management Read More. How to Customize Embedded Business Intelligence For Your Business By @goqrvey [ 8 Min read ] Choosing the right analytics solution is important for empowering users to access valuable insights without leaving your application. Read More. Lumoz Supports Op Stack + ZK Fraud Proof, Initiating a New Paradigm in L2 Architecture By @lumoz [ 3 Min read ] Lumoz's Modular Compute Layer has pioneered a new Layer 2 architecture model, filling the gap in the current market for a mixed solution of ZK and OP. Read More. How Multiplatform Game Development Grows Your Audience: A Guide to Playing Globally By @stepico [ 4 Min read ] Game development for multiple platforms at once is key to winning over players globally and boosting your revenue. Learn how it's done in the article. Read More. AI Is Changing How Developers Learn: Here's What That Means By @fahimulhaq [ 7 Min read ] AI-powered learning for software developers is here to stay. Here's how we're building the learning platform of the future at Educative. Read More. Mastering Maps in Go: Everything You Need to Know By @smokfyz [ 21 Min read ] Learn about using maps in Go (golang), including associative arrays, hash maps, collision handling, and sync.Map, with practical code examples. Read More. Mastering Product Engagement: Amplifying Interaction through Strategic Marketing (Part II) By @rachelecarraro [ 5 Min read ] Businesses can amplify the interaction between users and their tech product by leveraging strategic marketing. Here is how. Read More. Never Rely on UUID for Authentication: Generation Vulnerabilities and Best Practices By @mochalov [ 8 Min read ] The risks and best practices of using UUIDs for authentication, uncovering vulnerabilities, and secure implementation strategies. Read More. EigenLayer Airdrop Has Highlighted the Problems in the Crypto Market By @dariavolkova [ 6 Min read ] Eigen Layer airdrop illustrates a mismatch in users' expectations and market conditions. Why is the community angry with the biggest Ethereum restaking platform Read More. 7 Ways to Make Use of Llama-3 for Free By @naeomiee [ 4 Min read ] Discover the power of LLaMA-3 without breaking the bank! Learn 7 ways to utilize this advanced AI model for free, from text generation to creative projects. Read More. The Quietest in the Room: How Being Observant Cultivates Lifelong Success By @benoitmalige [ 10 Min read ] Discover how embracing silence and observance can transform your communication and open up a world of opportunities previously overshadowed by noise. Read More. Is Google's Search Ranking and AI Bias a Total Disaster? Let's See What Google Gemini Thinks By @egorkaleynik [ 5 Min read ] Uncover the harsh truth behind search ranking. I've had a conversation with Google's AI, Gemini, revealing ranking flaws where valuable content gets buried. Read More. Interview with Dr. Yonatan Sompolinsky of Kaspa By @mickeymaler [ 21 Min read ] Inclusive interview with Dr. Yonatan Sompolinsky of Kaspa, written for the book called "Kaspa: From Ghost to Knight, off to heal the blockchain's plight." Read More. The Human Roots of Rising Fascism By @kitthirasaki [ 7 Min read ] The rise of fascism in the US and Europe is driven by deep-seated human needs for comfort, significance, and belonging in the face of rapid change. Read More. 🧑💻 What happened in your world this week? It's been said that writing can help consolidate technical knowledge, establish credibility, and contribute to emerging community standards. Feeling stuck? We got you covered ⬇️⬇️⬇️ ANSWER THESE GREATEST INTERVIEW QUESTIONS OF ALL TIME We hope you enjoy this worth of free reading material. Feel free to forward this email to a nerdy friend who'll love you for it. See you on Planet Internet! With love, The HackerNoon Team ✌️

The TechBeat: Checklist for FinTech Product Growth:...
How are you, hacker?
🪐Want to know what's trending right now?:
The Techbeat...
Source: Hacker Noon
CHM Malware Stealing User Information Being Distributed in Korea

AhnLab SEcurity intelligence Center (ASEC) has recently discovered circumstances of a CHM malware strain that steals user information being distributed to Korean users. The distributed CHM is a type that has been constantly distributed in various formats such as LNK, DOC, and OneNote from the past. A slight change to the operation process was observed in the recent samples. The overall execution flow is shown in Figure 1. The malware is a type that uses multiple scripts to ultimately send... The post CHM Malware Stealing User Information Being Distributed in Korea appeared first on ASEC BLOG.

CHM Malware Stealing User Information Being Distributed...
AhnLab SEcurity intelligence Center (ASEC) has recently discovered circumstances...
Source: AhnLab