Search results for ACM
Using Scanned Mesh Data for Auto-Digitized 3D Modeling: Conclusion & Future Work and References
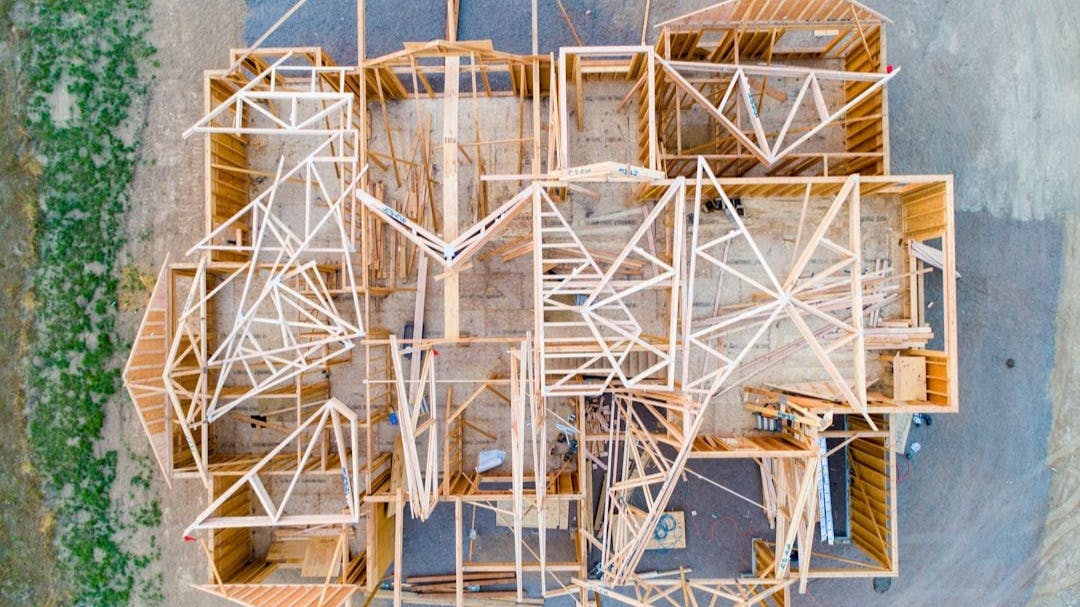
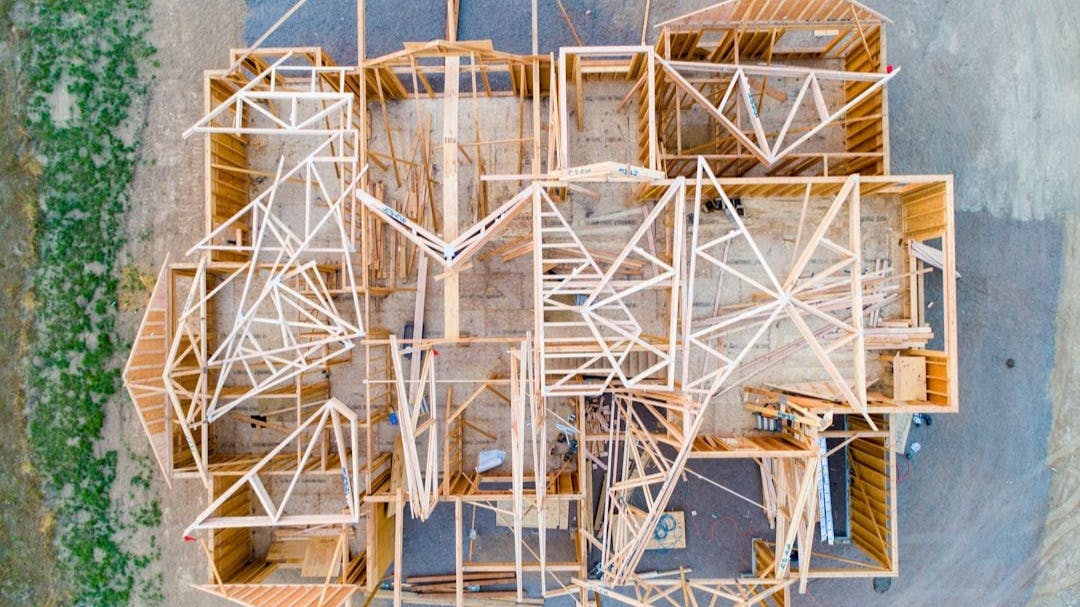
:::info Authors: (1) Ritesh Sharma, University Of California, Merced, USA rsharma39@ucmerced.edu; (2) Eric Bier, Palo Alto Research Center, USA bier@parc.com; (3) Lester Nelson, Palo Alto Research Center, USA lnelson@parc.com; (4) Mahabir Bhandari, Oak Ridge National Laboratory, USA bhandarims@ornl.gov; (5) Niraj Kunwar, Oak Ridge National Laboratory, USA kunwarn1@ornl.gov. ::: Table of Links Abstract and Intro Related Work Methodology Experiments Conclusion & Future work and References 5 Conclusion & Future work In summary, our new approach for generating floor plans from triangle mesh data collected by augmented reality (AR) headsets produces two styles: a detailed pen-and-ink style and a simplified drafting style. Our algorithms align the mesh data with primary coordinate axes to produce tidy floor plans with vertical and horizontal walls, while also allowing for the removal of ceilings and floors and the separation of multi-story buildings into individual stories. Our approach integrates with AR, supporting the addition of synthetic objects to physical geometry and providing a detailed 3D model and floor plan. Potential applications include navigation, interior design, furniture placement, facility management, building construction, and HVAC design. Moving forward, we plan to enable support for sloping ceilings, automate wall and door detection, and integrate with other tools such as energy simulators. Finally, we plan to compare our approach with existing state-of-the-art methods in terms of accuracy and computational time. We also plan to explore the applicability of block-based DBScan for 3D reconstruction from incomplete scans. Our approach has the potential to revolutionize the way we generate and visualize floor plans. References Adan, A., Huber, D.: 3d reconstruction of interior wall surfaces under occlusion and clutter. In: 2011 International Conference on 3D Imaging, Modeling, Processing, Visualization and Transmission. pp. 275–281 (2011). https://doi.org/10.1109/3DIMPVT.2011.42 Arikan, M., Schwärzler, M., Flöry, S., Wimmer, M., Maierhofer, S.: O-snap: Optimization-based snapping for modeling architecture. ACM Trans. Graph. 32(1) (feb 2013). https://doi.org/10.1145/2421636.2421642 Budroni, A., Boehm, J.: Automated 3d reconstruction of interiors from point clouds. International Journal of Architectural Computing 8(1), 55–73 (2010). https://doi.org/10.1260/1478-0771.8.1.55 Cabral, R.S., Furukawa, Y.: Piecewise planar and compact floorplan reconstruction from images. 2014 IEEE Conference on Computer Vision and Pattern Recognition pp. 628–635 (2014) Cai, R., Li, H., Xie, J., Jin, X.: Accurate floorplan reconstruction using geometric priors. Computers & Graphics 102, 360-369 (2022). https://doi.org/10.1016/j.cag.2021.10.011 Chen, J., Liu, C., Wu, J., Furukawa, Y.: Floor-sp: Inverse cad for floorplans by sequential room-wise shortest path. In: The IEEE International Conference on Computer Vision (ICCV) (2019) Chen, N., Lu, Z., Yu, X., Yang, L., Xu, P., Fan, Y.: Augmented reality-based home interaction layout and evaluation. In: Computer Graphics International Conference. pp. 395–406. Springer (2022) Dasgupta, S., Fang, K., Chen, K., Savarese, S.: Delay: Robust spatial layout estimation for cluttered indoor scenes. In: 2016 IEEE Conference on Computer Vision and Pattern Recognition (CVPR). pp. 616–624 (2016). https://doi.org/10.1109/CVPR.2016.73 Furukawa, Y., Curless, B., Seitz, S.M., Szeliski, R.: Reconstructing building interiors from images. In: 2009 IEEE 12th International Conference on Computer Vision. pp. 80–87 (2009). https://doi.org/10.1109/ICCV.2009.5459145 Gao, R., Zhao, M., Ye, T., Ye, F., Wang, Y., Bian, K., Wang, T., Li, X.: Jigsaw: Indoor floor plan reconstruction via mobile crowdsensing. In: Proceedings of the 20th Annual International Conference on Mobile Computing and Networking. p. 249–260. MobiCom '14, Association for Computing Machinery, New York, NY, USA (2014). https://doi.org/10.1145/2639108.2639134 Hsiao, C.W., Sun, C., Sun, M., Chen, H.T.: Flat2layout: Flat representation for estimating layout of general room types. ArXiv abs/1905.12571 (2019) Ikehata, S., Yang, H., Furukawa, Y.: Structured indoor modeling. In: 2015 IEEE International Conference on Computer Vision (ICCV). pp. 1323–1331 (2015). https://doi.org/10.1109/ICCV.2015.156 Kruzhilov, I., Romanov, M., Babichev, D., Konushin, A.: Double refinement network for room layout estimation. In: Palaiahnakote, S., Sanniti di Baja, G., Wang, L., Yan, W.Q. (eds.) Pattern Recognition. pp. 557–568. Springer International Publishing, Cham (2020) Lee, C.Y., Badrinarayanan, V., Malisiewicz, T., Rabinovich, A.: Roomnet: Endto-end room layout estimation. 2017 IEEE International Conference on Computer Vision (ICCV) pp. 4875–4884 (2017) Liu, C., Wu, J., Furukawa, Y.: Floornet: A unified framework for floorplan reconstruction from 3d scans. In: ECCV (2018) Liu, H., Yang, Y.L., AlHalawani, S., Mitra, N.J.: Constraint-aware interior layout exploration for precast concrete-based buildings. Visual Computer (CGI Special Issue) (2013) McNeel, R., et al.: Rhinoceros 3d, version 6.0. Robert McNeel & Associates, Seattle, WA (2010) Microsoft: Spatial mapping. https://docs.microsoft.com/en-us/windows/mixed-reality/spatial-mapping (2022) Monszpart, A., Mellado, N., Brostow, G.J., Mitra, N.J.: Rapter: Rebuilding manmade scenes with regular arrangements of planes. ACM Trans. Graph. 34(4) (jul 2015). https://doi.org/10.1145/2766995 Mura, C., Mattausch, O., Pajarola, R.: Piecewise-planar reconstruction of multiroom interiors with arbitrary wall arrangements. Computer Graphics Forum 35(7), 179–188 (2016). https://doi.org/https://doi.org/10.1111/cgf.13015 Murali, S., Speciale, P., Oswald, M.R., Pollefeys, M.: Indoor scan2bim: Building information models of house interiors. In: 2017 IEEE/RSJ International Conference on Intelligent Robots and Systems (IROS). pp. 6126–6133 (2017). https://doi. org/10.1109/IROS.2017.8206513 Okorn, B., Xiong, X., Akinci, B.: Toward automated modeling of floor plans. In: In Proceedings of the symposium on 3D data processing, visualization and transmission. vol. 2 (2010) Pintore, G., Gobbetti, E.: Effective mobile mapping of multi-room indoor structures. The visual computer 30(6-8), 707–716 (2014) Pintore, G., Mura, C., Ganovelli, F., Fuentes-Perez, L.J., Pajarola, R., Gobbetti, E.: State-of-the-art in Automatic 3D Reconstruction of Structured Indoor Environments. Computer Graphics Forum (2020). https://doi.org/10.1111/cgf.14021 Ramakrishnan, S.K., Gokaslan, A., Wijmans, E., Maksymets, O., Clegg, A., Turner, J.M., Undersander, E., Galuba, W., Westbury, A., Chang, A.X., Savva, M., Zhao, Y., Batra, D.: Habitat-matterport 3d dataset (HM3d): 1000 large-scale 3d environments for embodied AI. In: Thirty-fifth Conference on Neural Information Processing Systems Datasets and Benchmarks Track (Round 2) (2021), https://openreview.net/forum?id=-v4OuqNs5P Turner, E., Zakhor, A.: Watertight as-built architectural floor plans generated from laser range data. In: 2012 Second International Conference on 3D Imaging, Modeling, Processing, Visualization Transmission. pp. 316–323 (2012). https: //doi.org/10.1109/3DIMPVT.2012.80 Weinmann, M., Wursthorn, S., Weinmann, M., Hübner, P.: Efficient 3d mapping and modelling of indoor scenes with the microsoft hololens: A survey. PFG–Journal of Photogrammetry, Remote Sensing and Geoinformation Science 89(4), 319–333 (2021) Xiong, X., Adan, A., Akinci, B., Huber, D.: Automatic creation of semantically rich 3d building models from laser scanner data. Automation in Construction 31, 325–337 (2013). https://doi.org/10.1016/j.autcon.2012.10.006 Zhang, J., Kan, C., Schwing, A.G., Urtasun, R.: Estimating the 3d layout of indoor scenes and its clutter from depth sensors. In: 2013 IEEE International Conference on Computer Vision. pp. 1273–1280 (2013). https://doi.org/10.1109/ICCV.2013.161 Zou, C., Colburn, A., Shan, Q., Hoiem, D.: Layoutnet: Reconstructing the 3d room layout from a single rgb image. In: 2018 IEEE/CVF Conference on Computer Vision and Pattern Recognition (CVPR). pp. 2051–2059. IEEE Computer Society, Los Alamitos, CA, USA (jun 2018). https://doi.org/10.1109/CVPR.2018.00219 :::info This paper is available on arxiv under CC BY-NC-ND 4.0 DEED license. :::
Using Scanned Mesh Data for Auto-Digitized 3D Modeling:...
:::info
Authors:
(1) Ritesh Sharma, University Of California, Merced, USA rsharma39@ucmerced.edu;
(2)...
Source: Hacker Noon
Multi-EuP: Analysis of Bias in Information Retrieval - Conclusion, Limitations, and Ethics Statement

:::info This paper is available on arxiv under CC 4.0 license. Authors: (1) Jinrui Yang, School of Computing & Information Systems, The University of Melbourne (Email: jinruiy@student.unimelb.edu.au); (2) Timothy Baldwin, School of Computing & Information Systems, The University of Melbourne and Mohamed bin Zayed University of Artificial Intelligence, UAE (Email: (tbaldwin,trevor.cohn)@unimelb.edu.au); (3) Trevor Cohn, School of Computing & Information Systems, The University of Melbourne. ::: Table of Links Abstract and Intro Background and Related Work Multi-EuP Experiments and Findings Language Bias Discussion Conclusion, Limitations, Ethics Statement, Acknowledgements, References, and Appendix 6 Conclusion In this paper, we introduce Multi-EuP, a novel dataset for multilingual information retrieval across 24 languages, collected from European Parliament debates. The demographic information provided by the Multi-EuP dataset serves a dual purpose: not only does it contribute to multilingual retrieval tasks, but it also holds significant potential for advancing research in the realm of fairness and bias. This dataset can play a pivotal role in investigating issues of equitable representations and mitigation of biases within document ranking settings. Multi-EuP facilitates diverse information retrieval (IR) scenarios, encompassing one-vs-one, one-vs-many, and many-vs-many settings. We demonstrated the utility of Multi-EuP as a benchmark for evaluating both monolingual and multilingual IR. Our study reveals the presence of language bias in multilingual IR when employing BM25. We further validate the effectiveness of mitigating this bias through the strategic implementation of whitespace as a language tokenizer. We propose to conduct future work in three main areas. First, we intend to expand our investigation of language bias to encompass a broader range of ranking methods, including neural methods such as mDPR (Zhang et al., 2021), mColBERT (Lawrie et al., 2023) and PLAID-X(Santhanam et al., 2022). Second, we will expand the dataset by developing an automated API to retrieve data published by the European Parliament (EP), thereby ensuring realtime synchronization of our dataset. Lastly, our current experiments have explored language bias only, but we plan to further investigate gender bias, age bias, and nationality bias. Limitations The limitations of the Multi-EuP dataset are notable but navigable. Primarily, the temporal coverage of the dataset is confined to the past three years. This temporal constraint arises due to the fact that, preceding 2020, documents released by the EU were predominantly available in mono-lingual versions only. However, a potential remedy lies in the amalgamation of the Europarl (Koehn, 2005) collection, enabling a more comprehensive and holistic MultiEuP dataset. Furthermore, it is worth noting the domain skew of the dataset, in that Multi-EuP inevitably centers on political matters. While this presents challenges, particularly in terms of the intricate nuances of political language, it inherently serves as an excellent foundational stepping stone for delving into the intricacies of multilingual retrieval. We believe, however, that this dataset can serve as a launching pad for broader explorations encompassing crossdomain and open-domain transfer learning scenarios, thus contributing to the broader landscape of language understanding and retrieval. Ethics Statement The dataset contains publicly-available EP data that does not include personal or sensitive information, with the exception of information relating to public officeholders, e.g., the names of the active members of the European Parliament, European Council, or other official administration bodies. The collected data is licensed under the Creative Commons Attribution 4.0 International licence. [8] Acknowledgements This research was funded by Melbourne Research Scholarship and undertaken using the LIEF HPCGPGPU Facility hosted at the University of Melbourne. This facility was established with the assistance of LIEF Grant LE170100200. We would like to thank George Buchanan for providing valuable feedback. References Luiz Henrique Bonifacio, Israel Campiotti, Roberto de Alencar Lotufo, and Rodrigo Frassetto Nogueira. 2021. mMARCO: A multilingual version of MS MARCO passage ranking dataset. CoRR, abs/2108.13897. Ilias Chalkidis, Manos Fergadiotis, and Ion Androutsopoulos. 2021. MultiEURLEX - a multi-lingual and multi-label legal document classification dataset for zero-shot cross-lingual transfer. In Proceedings of the 2021 Conference on Empirical Methods in Natural Language Processing, pages 6974–6996, Online and Punta Cana, Dominican Republic. Association for Computational Linguistics. 8 https://eur-lex.europa.eu/cont Jonathan H. Clark, Eunsol Choi, Michael Collins, Dan Garrette, Tom Kwiatkowski, Vitaly Nikolaev, and Jennimaria Palomaki. 2020. TyDi QA: A benchmark for information-seeking question answering in typologically diverse languages. Transactions of the Association for Computational Linguistics, 8:454–470. Vladimir Karpukhin, Barlas Oguz, Sewon Min, Patrick Lewis, Ledell Wu, Sergey Edunov, Danqi Chen, and Wen-tau Yih. 2020. Dense passage retrieval for opendomain question answering. In Proceedings of the 2020 Conference on Empirical Methods in Natural Language Processing (EMNLP), pages 6769–6781, Online. Association for Computational Linguistics. Omar Khattab and Matei Zaharia. 2020. Colbert: Efficient and effective passage search via contextualized late interaction over BERT. CoRR, abs/2004.12832. Philipp Koehn. 2005. Europarl: A parallel corpus for statistical machine translation. In Proceedings of Machine Translation Summit X: Papers, pages 79–86, Phuket, Thailand. Dawn Lawrie, Eugene Yang, Douglas W. Oard, and James Mayfield. 2023. Neural approaches to multilingual information retrieval. arXiv cs.IR 2209.01335. Jimmy Lin, Xueguang Ma, Sheng-Chieh Lin, JhengHong Yang, Ronak Pradeep, and Rodrigo Nogueira. 2021. Pyserini: A Python toolkit for reproducible information retrieval research with sparse and dense representations. https://github.com/ castorini/pyserini. Tri Nguyen, Mir Rosenberg, Xia Song, Jianfeng Gao, Saurabh Tiwary, Rangan Majumder, and Li Deng. 2016. MS MARCO: A human generated machine reading comprehension dataset. CoRR, abs/1611.09268. Ella Rabinovich, Raj Nath Patel, Shachar Mirkin, Lucia Specia, and Shuly Wintner. 2017. Personalized machine translation: Preserving original author traits. In Proceedings of the 15th Conference of the European Chapter of the Association for Computational Linguistics: Volume 1, Long Papers, pages 1074–1084, Valencia, Spain. Association for Computational Linguistics. Razieh Rahimi, Azadeh Shakery, and Irwin King. 2015. Multilingual information retrieval in the language modeling framework. Information Retrieval Journal, 18:246–281. Keshav Santhanam, Omar Khattab, Christopher Potts, and Matei Zaharia. 2022. PLAID: An efficient engine for late interaction retrieval. In Proceedings of the 31st ACM International Conference on Information & Knowledge Management, CIKM '22, page 1747–1756, New York, NY, USA. Association for Computing Machinery. Jörg Tiedemann and Santhosh Thottingal. 2020. OPUSMT – building open translation services for the world. In Proceedings of the 22nd Annual Conference of the European Association for Machine Translation, pages 479–480, Lisboa, Portugal. European Association for Machine Translation. Eva Vanmassenhove and Christian Hardmeier. 2018. Europarl datasets with demographic speaker information. In Proceedings of the 21st Annual Conference of the European Association for Machine Translation, page 391, Alicante, Spain. Denny Vrandeciˇ c and Markus Krötzsch. 2014. ´ Wikidata: A free collaborative knowledge base. Communications of the ACM, 57:78–85. Konrad Wojtasik, Vadim Shishkin, Kacper Wołowiec, Arkadiusz Janz, and Maciej Piasecki. 2023. BEIRPL: Zero shot information retrieval benchmark for the Polish language. arXiv cs.IR 2305.19840. Peilin Yang, Hui Fang, and Jimmy Lin. 2017. Anserini: Enabling the use of lucene for information retrieval research. In Proceedings of the 40th International ACM SIGIR Conference on Research and Development in Information Retrieval, pages 1253–1256. Xinyu Zhang, Xueguang Ma, Peng Shi, and Jimmy Lin. 2021. Mr. TyDi: A multi-lingual benchmark for dense retrieval. arXiv cs.CL 2108.08787. A. Appendix [8] https://eur-lex.europa.eu/content/ legal-notice/legal-notice.html
Computational Linguistics dataset Language Bias machine translation

Multi-EuP: Analysis of Bias in Information Retrieval...
:::info
This paper is available on arxiv under CC 4.0 license.
Authors:
(1) Jinrui...
Source: Hacker Noon
Navigating Complex Search Tasks with AI Copilots: The Undiscovered Country and References

:::info This paper is available on arxiv under CC 4.0 license. Authors: (1) Ryen W. White, Microsoft Research, Redmond, WA, USA. ::: Table of Links Abstract and Taking Search to task AI Copilots Challenges Opportunities The Undiscovered Country and References 5 THE UNDISCOVERED COUNTRY AI copilots will transform how we search. Tasks are central to people's lives and more support is needed for complex tasks in search settings. Some limited support for these tasks already exists in search engines, but copilots will expand the task frontier to make more tasks actionable and address the “last mile” in search interaction: task completion [58]. Moving forward, search providers should invest in “better together” experiences that utilize copilots plus traditional search, make these joint experiences more seamless for searchers, and add more support for their use in practice, e.g., help people to quickly understand copilot capabilities and potential and/or recommend the best modality for the current task or task stage. This includes experiences where both modalities are offered separately and can be selected by searchers and those where there is unification and the selection happens automatically based on the query and the conversation context. The foundation models that power copilots have other search-related applications, e.g., for generating and applying intent taxonomies [43] or for evaluation [19]. We must retain a continued focus on human-AI cooperation, where searchers stay in control while the degree of system support increases as needed [44], and on AI safety. Searchers need to be able to trust copilots in general but also be able to verify their answers with minimal effort. Overall, the future is bright for IR, and AI research in general, with the advent of generative AI and the copilots that build upon it. Copilots will help augment and empower searchers in their information seeking journeys. Computer science researchers and practitioners should embrace this new era of assistive agents and engage across the full spectrum of exciting practical and scientific opportunities, both within information seeking as we focused on here, and onwards into other important domains such as personal productivity [5] and scientific discovery [22]. REFERENCES [1] Eugene Agichtein, Ryen W White, Susan T Dumais, and Paul N Bennet. 2012. Search, interrupted: understanding and predicting search task continuation. In Proceedings of the 35th international ACM SIGIR conference on Research and development in information retrieval. 315-324. [2] Marcia J Bates. 1990. Where should the person stop and the information search interface start? Information Processing & Management 26, 5 (1990), 575–591. [3] Nicholas J Belkin. 1980. Anomalous states of knowledge as a basis for information retrieval. Canadian journal of information science 5, 1 (1980), 133–143. [4] Paul N Bennett, Ryen W White, Wei Chu, Susan T Dumais, Peter Bailey, Fedor Borisyuk, and Xiaoyuan Cui. 2012. Modeling the impact of short-and long-term behavior on search personalization. In Proceedings of the 35th international ACM SIGIR conference on Research and development in information retrieval. 185–194. [5] Christian Bird, Denae Ford, Thomas Zimmermann, Nicole Forsgren, Eirini Kalliamvakou, Travis Lowdermilk, and Idan Gazit. 2022. Taking Flight with Copilot: Early insights and opportunities of AI-powered pair-programming tools. Queue 20, 6 (2022), 35–57. [6] Rishi Bommasani, Drew A Hudson, Ehsan Adeli, Russ Altman, Simran Arora, Sydney von Arx, Michael S Bernstein, Jeannette Bohg, Antoine Bosselut, Emma Brunskill, et al. 2021. On the opportunities and risks of foundation models. arXiv preprint arXiv:2108.07258 (2021). [7] Lucas Bourtoule, Varun Chandrasekaran, Christopher A Choquette-Choo, Hengrui Jia, Adelin Travers, Baiwu Zhang, David Lie, and Nicolas Papernot. 2021. Machine unlearning. In 2021 IEEE Symposium on Security and Privacy (SP). IEEE, 141–159. [8] Andrei Broder. 2002. A taxonomy of web search. In ACM Sigir forum, Vol. 36. ACM New York, NY, USA, 3–10. [9] Andrei Z Broder and Preston McAfee. 2023. Delphic Costs and Benefits in Web Search: A utilitarian and historical analysis. arXiv preprint arXiv:2308.07525 (2023). [10] Sébastien Bubeck, Varun Chandrasekaran, Ronen Eldan, Johannes Gehrke, Eric Horvitz, Ece Kamar, Peter Lee, Yin Tat Lee, Yuanzhi Li, Scott Lundberg, et al. 2023. Sparks of artificial general intelligence: Early experiments with gpt-4. arXiv preprint arXiv:2303.12712 (2023). [11] Katriina Byström and Kalervo Järvelin. 1995. Task complexity affects information seeking and use. Information processing & management 31, 2 (1995), 191–213. [12] Robert Capra and Jaime Arguello. 2023. How does AI chat change search behaviors? arXiv preprint arXiv:2307.03826 (2023). [13] Wei-Lin Chiang, Zhuohan Li, Zi Lin, Ying Sheng, Zhanghao Wu, Hao Zhang, Lianmin Zheng, Siyuan Zhuang, Yonghao Zhuang, Joseph E Gonzalez, et al. 2023. Vicuna: An open-source chatbot impressing gpt-4 with 90%* chatgpt quality. See https://vicuna. lmsys. org (accessed 14 April 2023) (2023). [14] Antonia Creswell and Murray Shanahan. 2022. Faithful reasoning using large language models. arXiv preprint arXiv:2208.14271 (2022). [15] Brenda Dervin. 1998. Sense-making theory and practice: An overview of user interests in knowledge seeking and use. Journal of knowledge management 2, 2 (1998), 36–46. [16] Jacob Devlin, Ming-Wei Chang, Kenton Lee, and Kristina Toutanova. 2018. Bert: Pre-training of deep bidirectional transformers for language understanding. arXiv preprint arXiv:1810.04805 (2018). [17] Karl Duncker and Lynne S Lees. 1945. On problem-solving. Psychological monographs 58, 5 (1945), i. [18] Brad Everman, Trevor Villwock, Dayuan Chen, Noe Soto, Oliver Zhang, and Ziliang Zong. 2023. Evaluating the Carbon Impact of Large Language Models at the Inference Stage. In 2023 IEEE International Performance, Computing, and Communications Conference (IPCCC). IEEE, 150–157. [19] Guglielmo Faggioli, Laura Dietz, Charles LA Clarke, Gianluca Demartini, Matthias Hagen, Claudia Hauff, Noriko Kando, Evangelos Kanoulas, Martin Potthast, Benno Stein, et al. 2023. Perspectives on Large Language Models for Relevance Judgment. In Proceedings of the 2023 ACM SIGIR International Conference on Theory of Information Retrieval. 39–50. [20] Jianfeng Gao, Chenyan Xiong, Paul Bennett, and Nick Craswell. 2023. Neural Approaches to Conversational Information Retrieval. Vol. 44. Springer Nature. [21] Ahmed Hassan Awadallah, Ryen W White, Patrick Pantel, Susan T Dumais, and Yi-Min Wang. 2014. Supporting complex search tasks. In Proceedings of the 23rd ACM international conference on conference on information and knowledge management. 829–838. [22] Tom Hope, Doug Downey, Daniel S Weld, Oren Etzioni, and Eric Horvitz. 2023. A computational inflection for scientific discovery. Commun. ACM 66, 8 (2023), 62–73. [23] Peter Ingwersen and Kalervo Järvelin. 2005. The turn: Integration of information seeking and retrieval in context. Vol. 18. Springer Science & Business Media. [24] Ziwei Ji, Nayeon Lee, Rita Frieske, Tiezheng Yu, Dan Su, Yan Xu, Etsuko Ishii, Ye Jin Bang, Andrea Madotto, and Pascale Fung. 2023. Survey of hallucination in natural language generation. Comput. Surveys 55, 12 (2023), 1–38. [25] Thorsten Joachims. 2002. Optimizing search engines using clickthrough data. In Proceedings of the eighth ACM SIGKDD international conference on Knowledge discovery and data mining. 133–142. [26] Jeonghyun Kim. 2006. Task difficulty as a predictor and indicator of web searching interaction. In CHI'06 extended abstracts on human factors in computing systems. 959–964. [27] David R Krathwohl. 2002. A revision of Bloom's taxonomy: An overview. Theory into practice 41, 4 (2002), 212–218. [28] Patrick Lewis, Ethan Perez, Aleksandra Piktus, Fabio Petroni, Vladimir Karpukhin, Naman Goyal, Heinrich Küttler, Mike Lewis, Wen-tau Yih, Tim Rocktäschel, et al. 2020. Retrieval-augmented generation for knowledge-intensive nlp tasks. Advances in Neural Information Processing Systems 33 (2020), 9459–9474. [29] Yuelin Li and Nicholas J Belkin. 2008. A faceted approach to conceptualizing tasks in information seeking. Information processing & management 44, 6 (2008), 1822–1837. [30] Yuanchun Li and Oriana Riva. 2021. Glider: A reinforcement learning approach to extract UI scripts from websites. In Proceedings of the 44th International ACM SIGIR Conference on Research and Development in Information Retrieval. 1420–1430. [31] Paul Pu Liang, Chiyu Wu, Louis-Philippe Morency, and Ruslan Salakhutdinov. 2021. Towards understanding and mitigating social biases in language models. In International Conference on Machine Learning. PMLR, 6565–6576. [32] Gary Marchionini. 2006. Exploratory search: from finding to understanding. Commun. ACM 49, 4 (2006), 41–46. [33] James Mayfield, Eugene Yang, Dawn Lawrie, Samuel Barham, Orion Weller, Marc Mason, Suraj Nair, and Scott Miller. 2023. Synthetic Cross-language Information Retrieval Training Data. arXiv preprint arXiv:2305.00331 (2023). [34] Subhabrata Mukherjee, Arindam Mitra, Ganesh Jawahar, Sahaj Agarwal, Hamid Palangi, and Ahmed Awadallah. 2023. Orca: Progressive learning from complex explanation traces of gpt-4. arXiv preprint arXiv:2306.02707 (2023). [35] Marc Najork. 2023. Generative Information Retrieval. In Proceedings of the 46th International ACM SIGIR Conference on Research and Development in Information Retrieval. 1–1. [36] Alexandra Olteanu, Jean Garcia-Gathright, Maarten de Rijke, Michael D Ekstrand, Adam Roegiest, Aldo Lipani, Alex Beutel, Alexandra Olteanu, Ana Lucic, AnaAndreea Stoica, et al. 2021. FACTS-IR: fairness, accountability, confidentiality, transparency, and safety in information retrieval. In ACM SIGIR Forum, Vol. 53. ACM New York, NY, USA, 20–43. [37] Soo Young Rieh, Kevyn Collins-Thompson, Preben Hansen, and Hye-Jung Lee. 2016. Towards searching as a learning process: A review of current perspectives and future directions. Journal of Information Science 42, 1 (2016), 19–34. [38] Shawon Sarkar and Chirag Shah. 2021. An integrated model of task, information needs, sources and uncertainty to design task-aware search systems. In Proceedings of the 2021 ACM SIGIR International Conference on Theory of Information Retrieval. 83–92. [39] Reijo Savolainen. 2012. Expectancy-value beliefs and information needs as motivators for task-based information seeking. Journal of Documentation 68, 4 (2012), 492–511. [40] Timo Schick, Jane Dwivedi-Yu, Roberto Dessì, Roberta Raileanu, Maria Lomeli, Luke Zettlemoyer, Nicola Cancedda, and Thomas Scialom. 2023. Toolformer: Language models can teach themselves to use tools. arXiv preprint arXiv:2302.04761 (2023). [41] Chirag Shah. 2023. Generative AI and the Future of Information Access. In Proceedings of the 32nd ACM International Conference on Information and Knowledge Management (Birmingham, United Kingdom) (CIKM '23). Association for Computing Machinery, New York, NY, USA, 3. https://doi.org/10.1145/3583780.3615317 [42] Chirag Shah, Ryen White, Paul Thomas, Bhaskar Mitra, Shawon Sarkar, and Nicholas Belkin. 2023. Taking search to task. In Proceedings of the 2023 Conference on Human Information Interaction and Retrieval. 1–13. [43] Chirag Shah, Ryen W White, Reid Andersen, Georg Buscher, Scott Counts, Sarkar Snigdha Sarathi Das, Ali Montazer, Sathish Manivannan, Jennifer Neville, Xiaochuan Ni, et al. 2023. Using Large Language Models to Generate, Validate, and Apply User Intent Taxonomies. arXiv preprint arXiv:2309.13063 (2023). [44] Ben Shneiderman. 2022. Human-centered AI. Oxford University Press. [45] Adish Singla, Ryen White, and Jeff Huang. 2010. Studying trailfinding algorithms for enhanced web search. In Proceedings of the 33rd international ACM SIGIR conference on Research and development in information retrieval. 443–450. [46] Jaime Teevan, Kevyn Collins-Thompson, Ryen W White, and Susan Dumais. 2014. Slow search. Commun. ACM 57, 8 (2014), 36–38. [47] Jaime Teevan, Susan T Dumais, and Eric Horvitz. 2005. Personalizing search via automated analysis of interests and activities. In Proceedings of the 28th annual international ACM SIGIR conference on Research and development in information retrieval. 449–456. [48] Jaime Teevan, Meredith Ringel Morris, and Steve Bush. 2009. Discovering and using groups to improve personalized search. In Proceedings of the second acm international conference on web search and data mining. 15–24. [49] Maartje ter Hoeve, Robert Sim, Elnaz Nouri, Adam Fourney, Maarten de Rijke, and Ryen W White. 2020. Conversations with documents: An exploration of document-centered assistance. In Proceedings of the 2020 Conference on Human Information Interaction and Retrieval. 43–52. [50] Paul Thomas, Seth Spielman, Nick Craswell, and Bhaskar Mitra. 2023. Large language models can accurately predict searcher preferences. arXiv preprint arXiv:2309.10621 (2023). [51] Randall H Trigg. 1988. Guided tours and tabletops: Tools for communicating in a hypertext environment. ACM Transactions on Information Systems (TOIS) 6, 4 (1988), 398–414. [52] Sarah K Tyler and Jaime Teevan. 2010. Large scale query log analysis of re-finding. In Proceedings of the third ACM international conference on Web search and data mining. 191–200. [53] Pertti Vakkari. 2001. A theory of the task-based information retrieval process: A summary and generalisation of a longitudinal study. Journal of documentation 57, 1 (2001), 44–60. [54] Pertti Vakkari. 2016. Searching as learning: A systematization based on literature. Journal of Information Science 42, 1 (2016), 7–18. [55] Nicholas Vincent. 2022. The Paradox of Reuse, Language Models Edition.https://nmvg.mataroa.blog/blog/the-paradox-of-reuse-language-modelsedition/. Accessed: 2023-09-12. [56] Yu Wang, Xiao Huang, and Ryen W White. 2013. Characterizing and supporting cross-device search tasks. In Proceedings of the sixth ACM international conference on Web search and data mining. 707–716. [57] Ryen W White. 2016. Interactions with search systems. Cambridge University Press. [58] Ryen W White. 2018. Opportunities and challenges in search interaction. Commun. ACM 61,12 (2018), 36–38. [59] Ryen W White. 2018. Skill discovery in virtual assistants. Commun. ACM 61, 11 (2018), 106–113. [60] Ryen W White. 2022. Intelligent futures in task assistance. Commun. ACM 65, 11 (2022), 35–39. [61] Ryen W. White. 2023. Tasks, Copilots, and the Future of Search. In Proceedings of the 46th International ACM SIGIR Conference on Research and Development in Information Retrieval (Taipei, Taiwan) (SIGIR '23). Association for Computing Machinery, New York, NY, USA, 5–6. https://doi.org/10.1145/3539618.3593069 [62] Ryen W White, Mikhail Bilenko, and Silviu Cucerzan. 2007. Studying the use of popular destinations to enhance web search interaction. In Proceedings of the 30th annual international ACM SIGIR conference on Research and development in information retrieval. 159–166. [63] Ryen W White, Wei Chu, Ahmed Hassan, Xiaodong He, Yang Song, and Hongning Wang. 2013. Enhancing personalized search by mining and modeling task behavior. In Proceedings of the 22nd international conference on World Wide Web. 1411–1420. [64] Ryen W White, Adam Fourney, Allen Herring, Paul N Bennett, Nirupama Chandrasekaran, Robert Sim, Elnaz Nouri, and Mark J Encarnación. 2019. Multi-device digital assistance. Commun. ACM 62, 10 (2019), 28–31. [65] Ryen W White, Ian Ruthven, and Joemon M Jose. 2005. A study of factors affecting the utility of implicit relevance feedback. In Proceedings of the 28th annual international ACM SIGIR conference on Research and development in information retrieval. 35–42. [66] Ryen W White, Ian Ruthven, Joemon M Jose, and CJ Van Rijsbergen. 2005. Evaluating implicit feedback models using searcher simulations. ACM Transactions on Information Systems (TOIS) 23, 3 (2005), 325–361. [67] Qingyun Wu, Gagan Bansal, Jieyu Zhang, Yiran Wu, Shaokun Zhang, Erkang Zhu, Beibin Li, Li Jiang, Xiaoyun Zhang, and Chi Wang. 2023. AutoGen: Enabling nextgen LLM applications via multi-agent conversation framework. arXiv preprint arXiv:2308.08155 (2023). [68] Iris Xie. 2008. Interactive information retrieval in digital environments. IGI global. [69] Jinyun Yan, Wei Chu, and Ryen W White. 2014. Cohort modeling for enhanced personalized search. In Proceedings of the 37th international ACM SIGIR conference on Research & development in information retrieval. 505–514. [70] Da Yu, Saurabh Naik, Arturs Backurs, Sivakanth Gopi, Huseyin A Inan, Gautam Kamath, Janardhan Kulkarni, Yin Tat Lee, Andre Manoel, Lukas Wutschitz, et al. 2021. Differentially private fine-tuning of language models. arXiv preprint arXiv:2110.06500 (2021). [71] Hamed Zamani, Susan Dumais, Nick Craswell, Paul Bennett, and Gord Lueck. 2020. Generating clarifying questions for information retrieval. In Proceedings of the web conference 2020. 418–428. [72] Jieyu Zhang, Ranjay Krishna, Ahmed H Awadallah, and Chi Wang. 2023. EcoAssistant: Using LLM Assistant More Affordably and Accurately. arXiv preprint arXiv:2310.03046 (2023). [73] Yi Zhang, Sujay Kumar Jauhar, Julia Kiseleva, Ryen White, and Dan Roth. 2021. Learning to decompose and organize complex tasks. In Proceedings of the 2021 Conference of the North American Chapter of the Association for Computational Linguistics: Human Language Technologies. 2726–2735. [74] Wenhao Zhu, Hongyi Liu, Qingxiu Dong, Jingjing Xu, Lingpeng Kong, Jiajun Chen, Lei Li, and Shujian Huang. 2023. Multilingual machine translation with large language models: Empirical results and analysis. arXiv preprint arXiv:2304.04675 (2023). [75] Daniel M Ziegler, Nisan Stiennon, Jeffrey Wu, Tom B Brown, Alec Radford, Dario Amodei, Paul Christiano, and Geoffrey Irving. 2019. Fine-tuning language models from human preferences. arXiv preprint arXiv:1909.08593 (2019).
ACM ACM SIGIR international ACM International Conference SIGIR conference

Navigating Complex Search Tasks with AI Copilots:...
:::info
This paper is available on arxiv under CC 4.0 license.
Authors:
(1) Ryen...
Source: Hacker Noon
Navigating Complex Search Tasks with AI Copilots: Abstract and Taking Search to task

:::info This paper is available on arxiv under CC 4.0 license. Authors: (1) Ryen W. White, Microsoft Research, Redmond, WA, USA. ::: Table of Links Abstract and Taking Search to task AI Copilots Challenges Opportunities The Undiscovered Country and References ABSTRACT As many of us in the information retrieval (IR) research community know and appreciate, search is far from being a solved problem. Millions of people struggle with tasks on search engines every day. Often, their struggles relate to the intrinsic complexity of their task and the failure of search systems to fully understand the task and serve relevant results [58]. The task motivates the search, creating the gap/problematic situation that searchers attempt to bridge/resolve and drives search behavior as they work through different task facets. Complex search tasks require more than support for rudimentary fact finding or re-finding. Research on methods to support complex tasks includes work on generating query and website suggestions [21, 62], personalizing and contextualizing search [4], and developing new search experiences, including those that span time and space [1, 64]. The recent emergence of generative artificial intelligence (AI) and the arrival of assistive agents, or copilots, based on this technology, has the potential to offer further assistance to searchers, especially those engaged in complex tasks [41, 61]. There are profound implications from these advances for the design of intelligent systems and for the future of search itself. This article, based on a keynote by the author at the 2023 ACM SIGIR Conference, explores these issues and charts a course toward new horizons in information access guided by AI copilots. ACM Reference Format: Ryen W. White. 2023. Navigating Complex Search Tasks with AI Copilots. Under review at REDACTED. October, 2023 1 TAKING SEARCH TO TASK Tasks are a critical part of people's daily lives. The market for dedicated task applications that help people with their “to do” tasks is likely to grow significantly (effectively triple in size) over the next few years.[1] There are many examples of such applications that can help both individuals (e.g., Microsoft To Do, Google Tasks, Todoist) and teams (e.g., Asana, Trello, Monday.com) tackle their tasks more effectively. Over time, these systems will increasingly integrate AI to better help their users capture, manage, and complete their tasks [60]. In information access scenarios such as search, tasks play an important role in motivating searching via gaps in knowledge and problematic situations [3, 15]. AI can be central in these search scenarios, too, especially in assisting with complex search tasks. 1.1 Tasks in Search Tasks drive the search process. The IR and information science communities have long studied tasks in search [42] and many information seeking models consider the role of task directly [3, 15]. Prior research has explored the different stages of task execution (e.g., pre-focus, focus formation, post-focus) [53], task levels [39], task facets [29], tasks defined on intents (e.g., informational, transactional, and navigational [8]; well-defined or ill-defined [23]; lookup, learn, or investigate [32]), the hierarchical structure of tasks [68], the characteristics of tasks, and the attributes of task searcher interaction, e.g., task difficulty and, of course, a focus in this article, task complexity [11, 26]. As a useful framing device to help conceptualize tasks and develop system support for them, tasks can be represented as trees comprising macrotasks (high level goals), subtasks (specific components of those goals), and actions (specific steps taken by searchers toward the completion of those components) [42]. Figure 1 presents an example of a “task tree” for a task involving an upcoming vacation to Paris, France. Examples of macrotasks, subtasks, and actions are included. Moves around this tree correspond to different task applications such as task recognition (up), task decomposition (down), and task prediction (across). Only actions (e.g., queries, clicks, and so on) are directly observable to traditional search engines. However, with recent advances in search copilots (more fully supporting natural language interactions via language understanding and language generation), more aspects of macrotasks and subtasks are becoming visible to search systems and more fully understood by those systems. Challenges in working with tasks include how to represent them within search systems, how to observe more task-relevant activity and content to develop richer task models, and how to develop task-oriented interfaces that place tasks and their completion at the forefront of user engagement. Task complexity deserves a special focus in this article given the challenges that searchers can still face with complex tasks and the significant potential of AI to help searchers tackle complex tasks. 1.2 Complex Search Tasks Recent estimates suggest that half of all Web searches are not answered.[2] Many of those searches are connected to complex search tasks. These tasks are ill-defined and/or multi-step, span multiple queries, sessions, and/or devices, and require deep engagement with search engines (many queries, backtracking, branching, etc.) to complete them [21]. Complex tasks also often have many facets and cognitive dimensions, and are closely connected to searcher characteristics such as domain expertise and task familiarity [38, 58]. To date, there have been significant attempts to support complex search tasks via humans (e.g., librarians, subject matter experts) and search systems (both general Web search engines and those tailored to specific industry verticals or domains). The main technological progress so far has been in areas such as query suggestion and contextual search, with new experiences also being developed that utilize multiple devices, provide cross-session support, and enable conversational search. We are now also seeing emerging search-related technologies in the area of generative AI [35]. Before proceeding, let us dive into these different types of existing and emerging search support for complex tasks in more detail. • Suggestions, personalization, and contextualization: Researchers and practitioners have long developed and deployed support such as query suggestion and trail suggestion, e.g., [21, 45], including providing guided tours [51] and suggesting popular trail destinations [62] as ways to find relevant resources. This coincides with work on contextual search and personalized search, e.g., [4, 47, 63], where search systems can use data from the current searcher such as session activity, location, reading level, and so on, and the searcher's long-term activity history, to provide more relevant results. Search engines may also use cohort activities to help with cold-start problems for new users and augment personal profiles for more established searchers [48, 69]. • Multi-device, cross-device, and cross-session: Devices have different capabilities and can be used in different settings. Multidevice experiences, e.g., [64], utilizing multiple devices simultaneously to better support complex tasks such as recipe preparation, auto repair, and home improvement that have been decomposed into steps manually or automatically [73]. Cross-device and cross-session support [1, 56] can help with ongoing/background searches for complex tasks that persist over space and time. For example, being able to predict task continuation can help with “slow search” applications that focus more on result quality than the near instantaneous retrieval of search results [46]. • Conversational experiences and generative AI: Natural language is an expressive and powerful means of communicating intentions and preferences with search systems. The introduction of clarification questions on search engine result pages (SERPs) [71], progress on conversational search [20], and even “conversations” with documents (where searchers can inquire about document content via natural language dialog) [49], enable these systems to engage more fully with searchers to better understand their tasks and goals. There are now many emerging opportunities to better understand and support more tasks via large-scale foundation models such as GPT-4[3] and DALL·E 3,[4] including offering conversational task assistance via chatbots such as ChatGPT.5 All of these advances, and others, have paved the way for the emergence of AI copilots, assistive agents that can help people tackle complex search tasks. [1] https://www.verifiedmarketresearch.com/product/task-management-softwaremarket/ [2] https://blogs.microsoft.com/blog/2023/02/07/reinventing-search-with-a-new-aipowered-microsoft-bing-and-edge-your-copilot-for-the-web/ [3] https://openai.com/gpt-4 [4] https://openai.com/dall-e-3 [5] https://openai.com/chatgpt

Navigating Complex Search Tasks with AI Copilots:...
:::info
This paper is available on arxiv under CC 4.0 license.
Authors:
(1) Ryen...
Source: Hacker Noon
Impact of the Net Neutrality Repeal on Communication Networks: Conclusions & References

:::info This paper is available on arxiv under CC 4.0 license. Authors: (1) Hatem A. Alharbi, CSchool of Electronic and Electrical Engineering, University of Leeds, LS2 9JT, United Kingdom; (2) Taisir E.H. Elgorashi, School of Electronic and Electrical Engineering, University of Leeds, LS2 9JT, United Kingdom; (3) Jaafar M.H. Elmirghani, School of Electronic and Electrical Engineering, University of Leeds, LS2 9JT, United Kingdom. ::: Table of Links Abstract & Introduction Related Works Repealing Net Neutrality Profit-Driven Model Results Conclusions & References Biographies V. CONCLUSIONS In this paper, we developed a MILP model to optimize the pricing scheme used by ISPs to charge CPs for delivering their video content under the repeal of net neutrality where ISPs can treat data intensive traffic less favorably. A techno-economic Mixed Integer Linear Programming (MILP) model is developed to maximize the ISP profit by optimizing the ISP pricing scheme to charge different classes of service differently subject to PED. We considered three classes of service that represent different data rate requirements of video content. The analysis addressed three CP delivery scenarios; cloud-based delivery, cloud-fog based delivery and fog-based delivery. The results show that the discriminatory pricing scheme can increase the ISPs profit by a factor of 8. The results also show that by influencing the way end-users consume data-intensive content, the core network traffic and consequently power consumption are reduced by up to 49% and 55%, respectively, compared to the net neutrality scenario. Acknowledgements The authors would like to acknowledge funding from the Engineering and Physical Sciences Research Council (EPSRC), INTERNET (EP/H040536/1), STAR (EP/K016873/1) and TOWS (EP/S016570/1) projects. The first author would like to acknowledge the Government of Saudi Arabia and Taibah University for funding his PhD scholarship. All data are provided in full in the results section of this paper. REFERENCES Cisco, “The Zettabyte Era: Trends and Analysis,” 2017. Ycharts.com, “AT&T Profit Margin (Quarterly),” 2018. [Online]. Available: https://ycharts.com/companies/T/profit_margin. [Accessed: 01-Aug-2018]. Ycharts, “Netflix Profit Margin (Quarterly),” 2018. [Online]. Available: https://ycharts.com/companies/NFLX/profit_margin. [Accessed: 01-Aug-2018]. T. Garrett, L. E. Setenareski, L. M. Peres, L. C. E. Bona, E. P. D. Jr, and A. Mislove, “Monitoring Network Neutrality : A Survey on Traffic Differentiation Detection,” IEEE Commun. Surv. Tutorials, no. c, pp. 1– 32, 2018. A. M. Kakhki, D. Choffnes, A. Mislove, and E. Katzbassett, “BingeOn Under the Microscope : Understanding T-Mobile ' s Zero-Rating Implementation,” Proc. 2016 Work. QoE-based Anal. Manag. Data Commun. Networks (Internet-QoE '16) ACM, pp. 43–48, 2016. J. S. Huang and B. Zhu, “Video Traffic Detection Method for Deep Packet Inspection,” Adv. CSIE, vol. 2, pp. 135– 140, 2012. Cisco Systems, “Traffic Profiling,” pp. 1–12. D. Tsilimantos, T. Karagkioules, A. Nogales-g, and S. Valentin, “Traffic profiling for mobile video streaming,” arXiv, pp. 1–7, 2017. W. Dai, J. W. Baek, and S. Jordan, “Neutrality between a vertically integrated cable provider and an over-the-top video provider,” J. Commun. Networks, vol. 18, no. 6, pp. 962–974, 2016. 10. Amazon, “Netflix Case Study - Amazon Web Services (AWS),” 2018. [Online]. Available: https://aws.amazon.com/solutions/case-studies/netflix/. [Accessed: 15-Aug-2018]. 11. AT&T, “AT&T Content Delivery Network (CDN) Services,” 2018. [Online]. Available: https://www.business.att.com/solutions/Family/cloud/cont ent-delivery-network/. [Accessed: 15-Aug-2018]. 12. [Comcast, “CDN - Comcast Technology Solutions,” 2018. [Online]. Available: https://www.comcasttechnologysolutions.com/resources/c omcast-cdn-one-sheet. [Accessed: 15-Aug-2018]. 13. “AT & T Switched Ethernet Classic ( ASE Classic ) and On-Demand ( ASEoD ).” 14. D. Grunwald, “The Internet Ecosystem : The Potential for Discrimination,” Fed. Commun. Law J., vol. 63, no. 2, pp. 411–443, 2011. 15. A. Odlyzko, “Network Neutrality, Search Neutrality, and the Never-ending Conflict between Efficiency and Fairness in Markets,” Rev. Netw. Econ., vol. 8, no. 1, pp. 40–60, 2009. 16. P. Nooren, A. Leurdijk, and N. van Eijk, “Net neutrality and the value chain for video,” Info, vol. 14, no. 6, pp. 45– 58, 2012. 17. R. T. B. Ma, J. Wang, and D. M. Chiu, “Paid prioritization and its impact on net neutrality,” IEEE J. Sel. Areas Commun., vol. 35, no. 2, pp. 367–379, 2017. 18. H.M.M., Ali, A.Q. Lawey, T.E.H. El-Gorashi, and J.M.H. Elmirghani, “Future Energy Efficient Data Centers With Disaggregated Servers,” IEEE/OSA Journal of Lightwave Technology, vol. 35, No. 24, pp. 5361 – 5380, 2017. 19. X. Dong, T. El-Gorashi, and J. Elmirghani, "Green IP Over WDM Networks With Data Centers," Lightwave Technology, Journal of, vol. 29, no. 12, pp. 1861-1880, June 2011. 20. N. I. Osman, T. El-Gorashi, L. Krug, and J. M. H. Elmirghani, “Energy Efficient Future High-Definition TV,” Journal of Lightwave Technology, vol. 32, no. 13, pp. 2364-2381, July 2014. 21. Lawey, T.E.H. El-Gorashi, and J.M.H. Elmirghani, “BitTorrent Content Distribution in Optical Networks,” IEEE/OSA Journal of Lightwave Technology, vol. 32, No. 21, pp. 3607 – 3623, 2014. 22. A.M. Al-Salim, A. Lawey, T.E.H. El-Gorashi, and J.M.H. Elmirghani, “Energy Efficient Big Data Networks: Impact of Volume and Variety,” IEEE Transactions on Network and Service Management, vol. 15, No. 1, pp. 458 - 474, 2018. 23. A.M. Al-Salim, A. Lawey, T.E.H. El-Gorashi, and J.M.H. Elmirghani, “Greening big data networks: velocity impact,” IET Optoelectronics, vol. 12, No. 3, pp. 126-135, 2018. 24. M.S. Hadi, A. Lawey, T.E.H. El-Gorashi, and J.M.H. Elmirghani, “Patient-Centric Cellular Networks Optimization using Big Data Analytics,” IEEE Access, pp. 49279 - 49296, vol. 7, 2019. 25. M.S. Hadi, A. Lawey, T.E.H. El-Gorashi, and J.M.H. Elmirghani, “Big Data Analytics for Wireless and Wired Network Design: A Survey, Elsevier Computer Networks, vol. 132, No. 2, pp. 180-199, 2018. 26. J. M. H. Elmirghani, T. Klein, K. Hinton, L. Nonde, A. Q. Lawey, T. E. H. El-Gorashi, M. O. I. Musa, and X. Dong, “GreenTouch GreenMeter core network energy-efficiency improvement measures and optimization,” IEEE/OSA Journal of Optical Communications and Networking, vol. 10, no. 2, pp. A250-A269, Feb 2018. 27. M. Musa, T.E.H. El-Gorashi and J.M.H. Elmirghani, “Bounds on GreenTouch GreenMeter Network Energy Efficiency,” IEEE/OSA Journal of Lightwave Technology, vol. 36, No. 23, pp. 5395-5405, 2018. 28. X. Dong, T.E.H. El-Gorashi and J.M.H. Elmirghani, “On the Energy Efficiency of Physical Topology Design for IP over WDM Networks,” IEEE/OSA Journal of Lightwave Technology, vol. 30, pp.1931-1942, 2012. 29. B. Bathula, M. Alresheedi, and J.M.H. Elmirghani, “Energy efficient architectures for optical networks,” Proc IEEE London Communications Symposium, London, Sept. 2009. 30. B. Bathula, and J.M.H. Elmirghani, “Energy Efficient Optical Burst Switched (OBS) Networks,” IEEE GLOBECOM'09, Honolulu, Hawaii, USA, November 30- December 04, 2009. 31. X. Dong, T.E.H. El-Gorashi and J.M.H. Elmirghani, “Green optical orthogonal frequency-division multiplexing networks,” IET Optoelectronics, vol. 8, No. 3, pp. 137 – 148, 2014. 32. X. Dong, T. El-Gorashi, and J. Elmirghani, “IP Over WDM Networks Employing Renewable Energy Sources,” Lightwave Technology, Journal of, vol. 29, no. 1, pp. 3-14, Jan 2011. 33. X. Dong, A.Q. Lawey, T.E.H. El-Gorashi, and J.M.H. Elmirghani, “Energy Efficient Core Networks,” Proc 16th IEEE Conference on Optical Network Design and Modelling (ONDM'12), 17-20 April, 2012, UK. 34. P. Mailé, G. Simon, and B. Tuffin, “Toward a net neutrality debate that conforms to the 2010s,” IEEE Commun. Mag., vol. 54, no. 3, pp. 94–99, 2016. 35. M. Musa, T.E.H. El-Gorashi and J.M.H. Elmirghani, “Bounds for Energy-Efficient Survivable IP Over WDM Networks with Network Coding,” IEEE/OSA Journal of Optical Communications and Networking, vol. 10, no. 5, pp. 471-481, 2018. 36. M. Musa, T.E.H. El-Gorashi and J.M.H. Elmirghani, “Energy Efficient Survivable IP-Over-WDM Networks With Network Coding,” IEEE/OSA Journal of Optical Communications and Networking, vol. 9, No. 3, pp. 207- 217, 2017. 37. L. Nonde, T.E.H. El-Gorashi, and J.M.H. Elmirghani, “Energy Efficient Virtual Network Embedding for Cloud Networks,” IEEE/OSA Journal of Lightwave Technology, vol. 33, No. 9, pp. 1828-1849, 2015. 38. A.N. Al-Quzweeni, A. Lawey, T.E.H. El-Gorashi, and J.M.H. Elmirghani, “Optimized Energy Aware 5G Network Function Virtualization,” IEEE Access, vol. 7, pp. 44939 - 44958, 2019. 39. Al-Azez, Z., Lawey, A., El-Gorashi, T.E.H., and Elmirghani, J.M.H., “Energy Efficient IoT Virtualization Framework with Peer to Peer Networking and Processing” IEEE Access, vol. 7, pp. 50697 - 50709, 2019. 40. R. S. Pindyck and D. L. Rubinfeld, Microeconomics. 2005. 41. R. Cadman, C. Dineen, and R. Cadman, “Price and Income Elasticity of Demand for Broadband Subscriptions : A Cross-Sectional Model of OECD Countries,” SPC Network, 19, pp. 3–8, 2009. 42. H. Galperin and C. A. Ruzzier, “Price elasticity of demand for broadband : Evidence from Latin America and the Caribbean,” Telecomm. Policy, vol. 37, pp. 429–438, 2013. 43. USAToday, “Interent bill too high,” 2018. 44. G. S. G. Shen and R. S. Tucker, “Energy-Minimized Design for IP Over WDM Networks,” IEEE/OSA J. Opt. Commun. Netw., vol. 1, no. 1, pp. 176–186, 2009. 45. Cisco, “United States - 2021 Forecast Highlights,” pp. 1– 6, 2016. 46. B. Insider, “Netflix subscribers over the years,” 2019. [Online]. Available: https://www.businessinsider.com/netflix-subscriberschart-2017-1?r=US&IR=T. [Accessed: 01-Jul-2018]. 47. J. Networks, “PTX1000, PTX10001, PTX10002, AND PTX10003 FIXEDCONFIGURATION PACKET TRANSPORT ROUTERS,” 2019. 48. Ycharts.com, “Comcast Corp Historical Profit Margin (Quarterly) Data,” 2018. [Online]. Available: https://ycharts.com/companies/CMCSA/profit_margin. [Accessed: 23-Aug-2018]. 49. J. Baliga, K. Hinton, and R. S. Tucker, “Energy Consumption of the Internet,” in COIN-ACOFT 2007 - Joint International Conference on the Optical Internet and the 32nd Australian Conference on Optical Fibre Technology, 2007, pp. 1–3. 50. AT&T, “AT&T's 38 Global Internet Data Centers.” [Online]. Available: https://www.business.att.com/content/productbrochures/e b_idcmap.pdf. [Accessed: 15-Aug-2018]. 51. Cisco System, “Cisco CRS-1 4-Slot Single-Shelf System,” 2014. 52. Cisco System, “Cisco ONS 15454 40 Gbps CP-DQPSK Full C-Band Tuneable Transponder Card.” 53. Oclaro, “OTS-4400 Regenerator,” 2014. 54. MRV, “EDFA Optical Amplifiers,” 2012. 55. “Intelligent Optical System 600,” Glimmerglass, 2013. [Online]. Available: http://www.glimmerglass.com/ products/intelligent-optical-systems/. [Accessed: 16-Mar2017]. 56. “GreenTouch Green Meter Research Study : Reducing the Net Energy Consumption in Communications Networks by up to 90 % by 2020,” White Pap., pp. 1–25, 2015. 57. A. Q. Lawey, T. E. H. El-Gorashi, and J. M. H. Elmirghani, “Distributed energy efficient clouds over core networks,” J. Light. Technol., vol. 32, no. 7, pp. 1261–1281, 2014.

Impact of the Net Neutrality Repeal on Communication...
:::info
This paper is available on arxiv under CC 4.0 license.
Authors:
(1) Hatem...
Source: Hacker Noon
Anonymous, Accountable Contract Wallet System With Account Abstraction: Conclusion & References

:::info This paper is available on arxiv under CC 4.0 license. Authors: (1) Kota Chin, University of Tsukuba, National Institute of Information and Communications Technology Japan; (2) Keita Emura, Kanazawa University, Japan National Institute of Information and Communications Technology Japan; (3) Kazumasa Omote, University of Tsukuba National Institute of Information and Communications Technology Japan. ::: Table of Links Abstract & Introduction Preliminaries Proposed Anonymous Yet Accountable Contract Wallet System Implementation Conclusion & References V. CONCLUSION In this paper, we proposed an anonymous yet accountable contract wallet system based on account abstraction and accountable ring signatures. The proposed system is implemented using Solidity for zkSync. Moreover, we discussed potential of the proposed system, e.g., medical information sharing and asset management. Since the current implementation results using Solidity show the required costs are expensive, our result here might be regarded as somewhat conceptual. However, to the best of our knowledge, no previous implementation result is known that confirms the cost to run an accountable ring signature scheme in Solidity to date, and we believe that our result can be seen as an important stepping stone to provide anonymity and accountability simultaneously in blockchain systems. Investigating other applications of the proposed system will be left to future work. The underlying account ring signature scheme does not provide post-quantum security due to the discrete logarithm-based construction. Thus, it is difficult to accept the current construction as a platform to manage large amounts of assets due to the progress of quantum computing. Because a post-quantum accountable ring signature scheme has been proposed in [7], it would be interesting to employ the scheme, precisely, how to implement it using Solidity is left to future work. Acknowledgment: The authors would like to thank Dr. Miyako Ohkubo (NICT) for her invaluable comments and suggestions. This work was supported by JSPS KAKENHI Grant Numbers JP21K11897 and JP22H03588. REFERENCES [1] Arrest of suspected developer of Tornado Cash. https://www.fiod.nl/arrest-of-suspected-developer-of-tornado-cash/. August 12, 2022. [2] StarkNet. https://starkware.co/starknet/. [3] zkSync. https://zksync.io/. [4] Jean-Philippe Aumasson, Daniel J. Bernstein, Ward Beullens, Christoph Dobraunig, Maria Eichlseder, Scott Fluhrer, Stefan-Lukas Gazdag, Andreas H ¨ulsing, Panos Kampanakis, Stefan K ¨olbl, Tanja Lange, Martin M. Lauridsen, Florian Mendel, Ruben Niederhagen, Christian Rechberger, Joost Rijneveld, Peter Schwabe, and Bas Westerbaan. SPHINCS+: Submission to the NIST post-quantum project, v.3.1. https://sphincs.org/data/sphincs+-r3.1-specification.pdf. [5] Asaph Azaria, Ariel Ekblaw, Thiago Vieira, and Andrew Lippman. MedRec: Using blockchain for medical data access and permission management. In 2016 2nd International Conference on Open and Big Data (OBD), pages 25–30, 2016. [6] Eli Ben-Sasson, Iddo Bentov, Yinon Horesh, and Michael Riabzev. Scalable, transparent, and post-quantum secure computational integrity. IACR Cryptol. ePrint Arch., page 46, 2018. [7] Ward Beullens, Samuel Dobson, Shuichi Katsumata, Yi-Fu Lai, and Federico Pintore. Group signatures and more from isogenies and lattices: Generic, simple, and efficient. In EUROCRYPT, pages 95–126, 2022. [8] Ward Beullens, Shuichi Katsumata, and Federico Pintore. Calamari and Falafl: Logarithmic (linkable) ring signatures from isogenies and lattices. In ASIACRYPT, pages 464–492, 2020. [9] Dmytro Bogatov, Angelo De Caro, Kaoutar Elkhiyaoui, and Bj ¨orn Tackmann. Anonymous transactions with revocation and auditing in hyperledger fabric. In CANS, pages 435–459, 2021. [10] Jonathan Bootle, Andrea Cerulli, Pyrros Chaidos, Essam Ghadafi, Jens Groth, and Christophe Petit. Short accountable ring signatures based on DDH. In ESORICS, pages 243–265, 2015. [11] Vitalik Buterin, Ansgar Dietrichs, Matt Garnett, Will Villanueva, and Sam Wilson. EIP-2938: Account Abstraction. https://eips.ethereum.org/EIPS/eip-2938, 2020. [12] Jan Camenisch, Manu Drijvers, and Maria Dubovitskaya. Practical ucsecure delegatable credentials with attributes and their application to blockchain. In ACM CCS, pages 683–699, 2017. [13] David Chaum and Eug`ene van Heyst. Group signatures. In EUROCRYPT, pages 257–265, 1991. [14] Aisling Connolly, J´er ˆome Deschamps, Pascal Lafourcade, and Octavio Perez-Kempner. Protego: Efficient, revocable and auditable anonymous credentials with applications to hyperledger fabric. In INDOCRYPT, pages 249–271, 2022. [15] L´eo Ducas, Eike Kiltz, Tancr`ede Lepoint, Vadim Lyubashevsky, Peter Schwabe, Gregor Seiler, and Damien Stehl´e. CRYSTALS-Dilithium: A lattice-based digital signature scheme. IACR Transactions on Cryptographic Hardware and Embedded Systems, 2018(1):238–268, 2018. [16] Kai Fan, Shangyang Wang, Yanhui Ren, Hui Li, and Yintang Yang. MedBlock: Efficient and secure medical data sharing via blockchain. Journal of Medical Systems, 42(8):136:1–136:11, 2018. [17] Tomilayo Fatokun, Avishek Nag, and Sachin Sharma. Towards a blockchain assisted patient owned system for electronic health records. Electronics, 10(5), 2021. [18] Pierre-Alain Fouque, Jeffrey Hoffstein, Paul Kirchner, Vadim Lyubashevsky, Thomas Pornin, Thomas Prest, Thomas Ricosset, Gregor Seiler, William Whyte, and Zhenfei Zhang. FALCON: Fast-fourier lattice-based compact signatures over NTRU. https://falcon-sign.info/falcon.pdf. [19] Tomoki Fujitani, Keita Emura, and Kazumasa Omote. A privacypreserving enforced bill collection system using smart contracts. In AsiaJCIS, pages 51–60. IEEE, 2021. [20] Merlin George and Anu Mary Chacko. MediTrans - patient-centric interoperability through blockchain. International Journal of Network Management, 32(3), 2022. [21] Jens Groth. Short non-interactive zero-knowledge proofs. In ASIACRYPT, pages 341–358, 2010. [22] Yiheng Liang. Identity verification and management of electronic health records with blockchain technology. In ICHI, pages 1–3. IEEE, 2019. [23] Joseph K. Liu, Victor K. Wei, and Duncan S. Wong. Linkable spontaneous anonymous group signature for ad hoc groups (extended abstract). In ACISP, pages 325–335, 2004. [24] Xingye Lu, Man Ho Au, and Zhenfei Zhang. Raptor: A practical latticebased (linkable) ring signature. In ACNS, pages 110–130, 2019. [25] Mohammad Moussa Madine, Ammar Ayman Battah, Ibrar Yaqoob, Khaled Salah, Raja Jayaraman, Yousof Al-Hammadi, Sasa Pesic, and Samer Ellahham. Blockchain for giving patients control over their medical records. IEEE Access, 8:193102–193115, 2020. [26] Abdullah Al Omar, Md. Zakirul Alam Bhuiyan, Anirban Basu, Shinsaku Kiyomoto, and Mohammad Shahriar Rahman. Privacy-friendly platform for healthcare data in cloud based on blockchain environment. Future Gener. Comput. Syst., 95:511–521, 2019. [27] Bryan Parno, Jon Howell, Craig Gentry, and Mariana Raykova. Pinocchio: nearly practical verifiable computation. Communications of the ACM, 59(2):103–112, 2016. [28] Sen Qiao, Varun Madathil, and Kemafor Anyanwu. Integrating group signatures in complex decentralized marketplace transactions for improved buyer privacy. In Blockchain, pages 139–148. IEEE, 2022. [29] Ronald L. Rivest, Adi Shamir, and Yael Tauman. How to leak a secret. In ASIACRYPT, pages 552–565, 2001. [30] Alex Roehrs, Cristiano Andre da Costa, and Rodrigo da Rosa Righi. OmniPHR: A distributed architecture model to integrate personal health records. Journal of Biomedical Informatics, 71:70–81, 2017. [31] Teppei Sato, Keita Emura, Tomoki Fujitani, and Kazumasa Omote. An anonymous trust-marking scheme on blockchain systems. IEEE Access, 9:108772–108781, 2021. [32] Kazuo Takaragi, Takashi Kubota, Sven Wohlgemuth, Katsuyuki Umezawa, and Hiroki Koyanagi. Secure revocation features in eKYC - privacy protection in central bank digital currency. IEICE Transactions on Fundamentals of Electronics, Communications and Computer Sciences, 106-A(3), 2023. [33] Qi Xia, Emmanuel Boateng Sifah, Kwame Omono Asamoah, Jianbin Gao, Xiaojiang Du, and Mohsen Guizani. MeDShare: Trust-less medical data sharing among cloud service providers via blockchain. IEEE Access, 5:14757–14767, 2017. [34] Shouhuai Xu and Moti Yung. Accountable ring signatures: A smart card approach. In CARDIS, pages 271–286, 2004.
Accountable Contract Contract Wallet Japan National Technology Japan

Anonymous, Accountable Contract Wallet System With...
:::info
This paper is available on arxiv under CC 4.0 license.
Authors:
(1) Kota...
Source: Hacker Noon
How to Secure your Heroku Apps with SSL Certificates for Custom Domains

This guide explains how to secure your Heroku applications with SSL certificates for custom domains using Automated Certificate Management (ACM) and Heroku SSL options. It covers the simplicity of ACM and the more robust features of Heroku SSL, ensuring data protection and web security for your hosted applications.
Automated Certificate Certificate Management Custom Domains Heroku SSL SSL Certificates

How to Secure your Heroku Apps with SSL Certificates...
This guide explains how to secure your Heroku applications with SSL certificates...
Source: Hacker Noon
The Power of Memes: The Pepper Robot as a Communicative Aid for Autistic Children - Conclusion

:::info This paper is available on arxiv under CC 4.0 license. Authors: (1) Linda Pigureddu, University of Turin, Italy, 332079@edu.unito.it; (2) Cristina Gena, Dept. of Computer Science, University of Turin, Italy, cristina.gena@unito.it. ::: Table of Links Introduction The Project Memes Conclusion and References CONCLUSION The analysis of the interactions and dialogues that took place during the therapeutic laboratory for autonomies endorsed with the inclusion of the Pepper robot provided an interesting perspective on the communication dynamics of children in the lab. The results obtained showed the effectiveness of the robot in promoting autonomy and functional acquisition, demonstrating that the therapeutic method based on assistive robotics is a valuable resource to support the rehabilitation needs of communication and social skills of autistic children. The analysis highlights new possibilities for their engagement and active participation as a co-designer, as we already experienced in the past with neuro-typical children [19], representing an innovative opportunity to promote the development and wellness of autistic people and opening to new perspectives for therapeutic intervention more aware of the needs of autistic minds. In conclusion, this paper highlights the need to provide the robot with the ability of adapt to the children's peculiarity and features and sharing her/his vocabulary, especially by recognizing and using memes during interactions, to inspire greater trust in children and allowing the use of common slang, already in use with classmates, allowing them to consider Pepper a peer and effectively insert it in the role of mediator. In addition, it would allow children to use a simplified type of communication during meetings to compensate for the typical communication deficits associated with autism spectrum disorders. In the future we will work in this directions (co-design, user's adaptations, using and recognizing memes during children-robot communication) having the robot able to communicate and express adapting to user tastes and preferences and and try again to field a real-world evaluation that takes into account the effectiveness of different levels of user adaptation [23]. REFERENCE [1] M. Biondi e M. Maj, DSM-5: diagnostic and statistical manual of mental disorders: text revision, 5. ed. Milano: Raffaello Cortina. [2] E. Hollander, R. Hagerman, e C. Ferretti, Textbook of Autism Spectrum Disorders, Second Edition. American Psychiatric Association Publishing, 2022. [3] ISS - Istituto superiore di sanità, «Osservatorio Nazionale Autismo», OssNA. https://osservatorionazionaleautismo.iss.it [4] P. Pennisi et al., «Autism and social robotics: A systematic review», Autism Research, vol. 9, fasc. 2, pp. 165–183, 2016, doi: 10.1002/aur.1527. [5] S. Shamsuddin, H. Yussof, S. Mohamed, e F. A. Hanapiah, «Design and Ethical Concerns in Robotic Adjunct Therapy Protocols for Children with Autism», Procedia Computer Science, vol. 42, pp. 9–16, gen. 2014, doi: 10.1016/j.procs.2014.11.027. [6] K. Dautenhahn e I. Werry, «Towards Interactive Robots in Autism Therapy: Background, Motivation and Challenges», Pragmatics & Cognition, vol. 12, pp. 1–35, giu. 2004, doi: 10.1075/pc.12.1.03dau. [7] C. Li, Q. Jia, e Y. Feng, «Human-Robot Interactoin Design for Robot-Assisted Intervention for Children with Autism Based on E-S Theory», in 2016 8th International Conference on Intelligent Human-Machine Systems and Cybernetics (IHMSC), Hangzhou, China: IEEE, ago. 2016, pp. 320–324. doi: 10.1109/IHMSC.2016.103. [8] A. Peca et al., «Robot Enhanced Therapy for Children with Autism Disorders: Measuring Ethical Acceptability», IEEE Technol. Soc. Mag., vol. 35, fasc. 2, pp. 54–66, giu. 2016, doi: 10.1109/MTS.2016.2554701. [9] B. Robins, K. Dautenhahn, e J. Dubowski, «Does appearance matter in the interaction of children with autism with a humanoid robot?», IS, vol. 7, fasc. 3, pp. 479–512, nov. 2006, doi:10.1075/is.7.3.16rob. [10] E. S. Kim, «Robots for social skills therapy in autism: evidence and designs toward clinical utility», 2013, doi: 10.13140/2.1.3038.2083. [11] «Autismo», Neuraxpharm Italia. https://www.neuraxpharm.com/it/disordini/autismo [12] L. Hull, K. V. Petrides, e W. Mandy, «The Female Autism Phenotype and Camouflaging: a Narrative Review», Rev J Autism Dev Disord, vol. 7, fasc. 4, pp. 306–317, dic. 2020, doi: 10.1007/s40489-020-00197-9. [13] D. Cohen et al., «NAO, a humanoid robot as a therapeutic mediator for young people with autism». [14] Cristina Gena, Claudio Mattutino, Andrea Maieli, Elisabetta Miraglio, Giulia Ricciardiello, Rossana Damiano, Alessandro Mazzei: Autistic Children's Mental Model of an Humanoid Robot. UMAP (Adjunct Publication) 2021: 128-129 [15] Rossana Damiano, Cristina Gena, Andrea Maieli, Claudio Mattutino, Alessandro Mazzei, Elisabetta Miraglio, Giulia Ricciardiello: UX Personas for Defining Robot's Character and Personality 213-216. IUI Workshops 2022: 213-216. [16] Cristina Gena, Claudio Mattutino, Stefania Brighenti, Andrea Meirone, Francesco Petriglia, Loredana Mazzotta, Federica Liscio, Matteo Nazzario, Valeria Ricci, Camilla Quarato, Cesare Pecone, Giuseppe Piccinni: et al., Sugar, Salt & Pepper - Humanoid robotics for autism, in Joint Proceedings of the ACM IUI 2021 Workshops co-located with 26th ACM Conference on Intelligent User Interfaces (ACM IUI 2021), College Station, United States, April 13-17, 2021, D. Glowacka e V. R. Krishnamurthy, A c. di, in CEUR Workshop Proceedings, vol. 2903. CEUR-WS.org, 2021. [17] Cristina Gena, Rossana Damiano, Claudio Mattutino, Alessandro Mazzei, Andrea Meirone, Loredana Mazzotta, Matteo Nazzario, Valeria Ricci, Stefania Brighenti, Federica Liscio, Francesco Petriglia: Preliminary results of a therapeutic lab for promoting autonomies in autistic children. arXiv, doi: 10.48550/arXiv.2305.02982. [18] B. C. Carbo, «The Use of Social Stories with Individuals with Autism Spectrum Disorders», University of Delaware ProQuest Dissertations Publishing, Newark, DE, 2005. [Online]. Disponibile su: https://udspace.udel.edu/server/api/core/bitstreams/cd5e8850-e57c-41d2-a7b4ac5e25a4b659/content [19] V. Cietto, C. Gena, I. Lombardi, C. Mattutino and C. Vaudano, "Co-designing with kids an educational robot," 2018 IEEE Workshop on Advanced Robotics and its Social Impacts (ARSO), Genova, Italy, 2018, pp. 139-140, doi: 10.1109/ARSO.2018.8625810. [20] A. Mousa, «Sherry Turkle, Reclaiming Conversation. The Power of Talk in a Digital Age», Questions de communication, fasc. 34, Art. fasc. 34, dic. 2018, doi:10.4000/questionsdecommunication.16891. [21] H.-M. Chiang e M. Carter, «Spontaneity of Communication in Individuals with Autism», J Autism Dev Disord, vol. 38, fasc. 4, pp. 693–705, apr. 2008, doi: 10.1007/s10803-007-0436-7. [22] Gena, C., Cena, F., Vernero, F., Grillo, P. The evaluation of a social adaptive website for cultural events. User Model User-Adap Inter 23, 89–137 (2013) https://doi.org/10.1007/s11257-012-9129-9 [23] Gena, Cristina, and Ilaria Torre. "The importance of adaptivity to provide onboard services: A preliminary evaluation of an adaptive tourist information service onboard vehicles." Applied Artificial Intelligence 18.6 (2004): 549-580.

The Power of Memes: The Pepper Robot as a Communicative...
:::info
This paper is available on arxiv under CC 4.0 license.
Authors:
(1) Linda...
Source: Hacker Noon
LTESniffer - An Open-source LTE Downlink/Uplink Eavesdropper
LTESniffer is An Open-source LTE Downlink/Uplink Eavesdropper It first decodes the Physical Downlink Control Channel (PDCCH) to obtain the Downlink Control Informations (DCIs) and Radio Network Temporary Identifiers (RNTIs) of all active users. Using decoded DCIs and RNTIs, LTESniffer further decodes the Physical Downlink Shared Channel (PDSCH) and Physical Uplink Shared Channel (PUSCH) to retrieve uplink and downlink data traffic. LTESniffer supports an API with three functions for security applications and research. Many LTE security research assumes a passive sniffer that can capture privacy-related packets on the air. However, non of the current open-source sniffers satisfy their requirements as they cannot decode protocol packets in PDSCH and PUSCH. We developed a proof-of-concept security API that supports three tasks that were proposed by previous works: 1) Identity mapping, 2) IMSI collecting, and 3) Capability profiling. Please refer to our paper for more details. LTESniffer in layman's terms LTESniffer is a tool that can capture the LTE wireless messages that are sent between a cell tower and smartphones connected to it. LTESniffer supports capturing the messages in both directions, from the tower to the smartphones, and from the smartphones back to the cell tower. LTESniffer CANNOT DECRYPT encrypted messages between the cell tower and smartphones. It can be used for analyzing unencrypted parts of the communication between the cell tower and smartphones. For example, for encrypted messages, it can allow the user to analyze unencrypted parts, such as headers in MAC and physical layers. However, those messages sent in plaintext can be completely analyzable. For example, the broadcast messages sent by the cell tower, or the messages at the beginning of the connection are completely visible. Ethical Consideration The main purpose of LTESniffer is to support security and analysis research on the cellular network. Due to the collection of uplink-downlink user data, any use of LTESniffer must follow the local regulations on sniffing the LTE traffic. We are not responsible for any illegal purposes such as intentionally collecting user privacy-related information. Features New Update Supports two USRP B-series for uplink sniffing mode. Please refer to LTESniffer-multi-usrp branch and its README for more details. Improved the DCI 0 detected in uplink. Fixed some bugs. LTESniffer is implemented on top of FALCON with the help of srsRAN library. LTESniffer supports: Real-time decoding LTE uplink-downlink control-data channels: PDCCH, PDSCH, PUSCH LTE Advanced and LTE Advanced Pro, up to 256QAM in both uplink and downlink DCI formats: 0, 1A, 1, 1B, 1C, 2, 2A, 2B Transmission modes: 1, 2, 3, 4 FDD only Maximum 20 MHz base station. Automatically detect maximum UL/DL modulation schemes of smartphones (64QAM/256QAM on DL and 16QAM/64QAM/256QAM on UL) Automatically detect physical layer configuration per UE. LTE Security API: RNTI-TMSI mapping, IMSI collecting, UECapability Profiling. Hardware and Software Requirement OS Requirement Currently, LTESniffer works stably on Ubuntu 18.04/20.04/22.04. Hardware Requirement Achieving real-time decoding of LTE traffic requires a high-performance CPU with multiple physical cores. Especially when the base station has many active users during the peak hour. LTESniffer was able to achieve real-time decoding when running on an Intel i7-9700K PC to decode traffic on a base station with 150 active users. The following hardware is recommended Intel i7 CPU with at least 8 physical cores At least 16Gb RAM 256 Gb SSD storage SDR LTESniffer requires different SDR for its uplink and downlink sniffing modes. To sniff only downlink traffic from the base station, LTESniffer is compatible with most SDRs that are supported by the srsRAN library (for example, USRP or BladeRF). The SDR should be connected to the PC via a USB 3.0 port. Also, it should be equipped with GPSDO and two RX antennas to decode downlink messages in transmission modes 3 and 4. On the other hand, to sniff uplink traffic from smartphones to base stations, LTESniffer needs to listen to two different frequencies (Uplink and Downlink) concurrently. To solve this problem, LTESniffer supports two options: Using a single USRP X310. USRP X310 has two Local Oscillators (LOs) for 2 RX channels, which can turn each RX channel to a distinct Uplink/Downlink frequency. To use this option, please refer to the main branch of LTESniffer. Using 2 USRP B-Series. LTESniffer utilizes 2 USRP B-series (B210/B200) for uplink and downlink separately. It achieves synchronization between 2 USRPs by using GPSDO for clock source and time reference. To use this option, please refer to the LTESniffer-multi-usrp branch of LTESniffer and its README. Installation Important note: To avoid unexpected errors, please follow the following steps on Ubuntu 18.04/20.04/22.04. Dependencies Important dependency: UHD library version >= 4.0 must be installed in advance (recommend building from source). The following steps can be used on Ubuntu 18.04. Refer to UHD Manual for full installation guidance. UHD dependencies: sudo apt updatesudo apt-get install autoconf automake build-essential ccache cmake cpufrequtils doxygen ethtool g++ git inetutils-tools libboost-all-dev libncurses5 libncurses5-dev libusb-1.0-0 libusb-1.0-0-dev libusb-dev python3-dev python3-mako python3-numpy python3-requests python3-scipy python3-setuptools python3-ruamel.yaml Clone and build UHD from source (make sure that the current branch is higher than 4.0) git clone https://github.com/EttusResearch/uhd.gitcd <uhd-repo-path>/hostmkdir buildcd buildcmake ../make -j 4make testsudo make installsudo ldconfig Download firmwares for USRPs: sudo uhd_images_downloader We use a 10Gb card to connect USRP X310 to PC, refer to UHD Manual [1], [2] to configure USRP X310 and 10Gb card interface. For USRP B210, it should be connected to PC via a USB 3.0 port. Test the connection and firmware (for USRP X310 only): sudo sysctl -w net.core.rmem_max=33554432sudo sysctl -w net.core.wmem_max=33554432sudo ifconfig <10Gb card interface> mtu 9000sudo uhd_usrp_probe srsRAN dependencies: sudo apt-get install build-essential git cmake libfftw3-dev libmbedtls-dev libboost-program-options-dev libconfig++-dev libsctp-dev LTESniffer dependencies: sudo apt-get install libglib2.0-dev libudev-dev libcurl4-gnutls-dev libboost-all-dev qtdeclarative5-dev libqt5charts5-dev Build LTESniffer from source: git clone https://github.com/SysSec-KAIST/LTESniffer.gitcd LTESniffermkdir buildcd buildcmake ../make -j 4 (use 4 threads) Usage LTESniffer has 3 main functions: Sniffing LTE downlink traffic from the base station Sniffing LTE uplink traffic from smartphones Security API After building from source, LTESniffer is located in <build-dir>/src/LTESniffer Note that before using LTESniffer on the commercial, one should have to check the local regulations on sniffing LTE traffic, as we explained in the Ethical Consideration. To figure out the base station and Uplink-Downlink band the test smartphone is connected to, install Cellular-Z app on the test smartphone (the app only supports Android). It will show the cell ID and Uplink-Downlink band/frequency to which the test smartphone is connected. Make sure that LTESniffer also connects to the same cell and frequency. General downlink sniffing sudo ./<build-dir>/src/LTESniffer -A 2 -W <number of threads> -f <DL Freq> -C -m 0example: sudo ./src/LTESniffer -A 2 -W 4 -f 1840e6 -C -m 0-A: number of antennas-W: number of threads-f: downlink frequency-C: turn on cell search-m: sniffer mode, 0 for downlink sniffing and 1 for uplink sniffing Note: to run LTESniffer with USRP B210 in the downlink mode, add option -a "num_recv_frames=512" to the command line. This option extends the receiving buffer for USRP B210 to achieve better synchronization. sudo ./<build-dir>/src/LTESniffer -A 2 -W <number of threads> -f <DL Freq> -C -m 0 -a "num_recv_frames=512"example: sudo ./src/LTESniffer -A 2 -W 4 -f 1840e6 -C -m 0 -a "num_recv_frames=512" General uplink sniffing Note: In the uplink sniffing mode, the test smartphones should be located nearby the sniffer, because the uplink signal power from UE is significantly weaker compared to the downlink signal from the base station. sudo ./<build-dir>/src/LTESniffer -A 2 -W <number of threads> -f <DL Freq> -u <UL Freq> -C -m 1example: sudo ./src/LTESniffer -A 2 -W 4 -f 1840e6 -u 1745e6 -C -m 1-u: uplink frequency Security API sudo ./<build-dir>/src/LTESniffer -A 2 -W <number of threads> -f <DL Freq> -u <UL Freq> -C -m 1 -z 3example: sudo ./src/LTESniffer -A 2 -W 4 -f 1840e6 -u 1745e6 -C -m 1 -z 3-z: 3 for turnning on 3 functions of sniffer, which are identity mapping, IMSI collecting, and UECapability profiling. 2 for UECapability profiling 1 for IMSI collecting 0 for identity mapping Specify a base station LTESniffer can sniff on a specific base station by using options -I <Phycial Cell ID (PCI)> -p <number of Physical Resource Block (PRB)>. In this case, LTESniffer does not do the cell search but connects directly to the specified cell. sudo ./<build-dir>/src/LTESniffer -A 2 -W <number of threads> -f <DL Freq> -I <PCI> -p <PRB> -m 0sudo ./<build-dir>/src/LTESniffer -A 2 -W <number of threads> -f <DL Freq> -u <UL Freq> -I <PCI> -p <PRB> -m 1example: sudo ./src/LTESniffer -A 2 -W 4 -f 1840e6 -u 1745e6 -I 379 -p 100 -m 1 The debug mode can be enabled by using option -d. In this case, the debug messages will be printed on the terminal. Output of LTESniffer LTESniffer provides pcap files in the output. The pcap file can be opened by WireShark for further analysis and packet trace. The name of downlink pcap file: sniffer_dl_mode.pcap, uplink pcap file: sniffer_ul_mode.pcap, and API pcap file: api_collector.pcap. The pcap files are located in the same directory LTESniffer has been executed. To enable the WireShark to analyze the decoded packets correctly, please refer to the WireShark configuration guide here. There are also some examples of pcap files in the link. Note: The uplink pcap file contains both uplink and downlink messages. On the WireShark, use this filter to monitor only uplink messages: mac-lte.direction == 0; or this filter to monitor only downlink messages: mac-lte.direction == 1. Application Note Distance for uplink sniffing The effective range for sniffing uplink is limited in LTESniffer due to the capability of the RF front-end of the hardware (i.e. SDR). The uplink signal power from UE is significantly weaker compared to the downlink signal because UE is a handheld device that optimizes battery usage, while the eNB uses sufficient power to cover a large area. To successfully capture the uplink traffic, LTESniffer can increase the strength of the signal power by i) being physically close to the UE, or ii) improving the signal reception capability with specialized hardware, such as a directional antenna, dedicated RF front-end, and signal amplifier. The information displayed on the terminal Downlink Sniffing Mode Processed 1000/1000 subframes: Number of subframes was processed by LTESniffer last 1 second. There are 1000 LTE subframes per second by design. RNTI: Radio Network Temporary Identifier of UEs. Table: The maximum modulation scheme that is used by smartphones in downlink. LTESniffer supports up to 256QAM in the downlink. Refer to our paper for more details. Active: Number of detected messages of RNTIs. Success: Number of successfully decoded messages over number of detected messages (Active). New TX, ReTX, HARQ, Normal: Statistic of new messages and retransmitted messages. This function is in development. W_MIMO, W_pinfor, Other: Number of messages with wrong radio configuration, only for debugging. Uplink Sniffing Mode Max Mod: The maximum modulation scheme that is used by smartphones in uplink. It can be 16/64/256QAM depending on the support of smartphones and the configuration of the network. Refer to our paper for more details. SNR: Signal-to-noise ratio (dB). Low SNR means the uplink signal quality from the smartphone is bad. One possible reason is the smartphone is far from the sniffer. DL-UL_delay: The average of time delay between downlink signal from the base station and uplink signal from the smartphone. Other Info: Information only for debugging. API Mode Detected Identity: The name of detected identity. Value: The value of detected identity. From Message: The name of the message that contains the detected identity. Credits We sincerely appreciate the FALCON and SRS team for making their great softwares available. BibTex Please refer to our paper for more details. @inproceedings{hoang:ltesniffer, title = {{LTESniffer: An Open-source LTE Downlink/Uplink Eavesdropper}}, author = {Hoang, Dinh Tuan and Park, CheolJun and Son, Mincheol and Oh, Taekkyung and Bae, Sangwook and Ahn, Junho and Oh, BeomSeok and Kim, Yongdae}, booktitle = {16th ACM Conference on Security and Privacy in Wireless and Mobile Networks (WiSec '23)}, year = {2023}} FAQ Q: Is it mandatory to use GPSDO with the USRP in order to run LTESniffer? A: GPSDO is useful for more stable synchronization. However, for downlink sniffing mode, LTESniffer still can synchronize with the LTE signal to decode the packets without GPSDO. For uplink sniffing mode, GPSDO is only required when using 2 USRP B-series, as it is the time and clock reference sources for synchrozation between uplink and downlink channels. Another uplink SDR option, using a single USRP X310, does not require GPSDO. Q: For downlink traffic, can I use a cheaper SDR? A: Technically, any SDRs supported by srsRAN library such as Blade RF can be used to run LTESniffer in the downlink sniffing mode. However, we only tested the downlink sniffing function of LTESniffer with USRP B210 and X310. Q: Is it illegal to use LTESniffer to sniff the LTE traffic? A: You should have to check the local regulations on sniffing (unencrypted) LTE traffic. Another way to test LTESniffer is setting up a personal LTE network by using srsRAN - an open-source LTE implementation in a Faraday cage. Q: Can LTESniffer be used to view the content of messages between two users? A: One can see only the "unencrypted" part of the messages. Note that the air traffic between the base station and users is mostly encrypted. Q: Is there any device identity exposed in plaintext in the LTE network? A: Yes, literature shows that there are multiple identities exposed, such as TMSI, GUTI, IMSI, and RNTI. Please refer to the academic literature for more details. e.g. Watching the Watchers: Practical Video Identification Attack in LTE Networks Download LTESniffer

LTESniffer - An Open-source LTE Downlink/Uplink Eavesdropper...
LTESniffer is An Open-source LTE Downlink/Uplink Eavesdropper It first decodes...
Source: KitPloit
Google Trust Services ACME API available to all users at no cost

David Kluge, Technical Program Manager, and Andy Warner, Product ManagerNobody likes preventable site errors, but they happen disappointingly often. The last thing you want your customers to see is a dreaded 'Your connection is not private' error instead of the service they expected to reach. Most certificate errors are preventable and one of the best ways to help prevent issues is by automating your certificate lifecycle using the ACME standard. Google Trust Services now offers our ACME API to all users with a Google Cloud account (referred to as “users” here), allowing them to automatically acquire and renew publicly-trusted TLS certificates for free. The ACME API has been available as a preview and over 200 million certificates have been issued already, offering the same compatibility as major Google services like google.com or youtube.com.

Google Trust Services ACME API available to all users...
David Kluge, Technical Program Manager, and Andy Warner, Product ManagerNobody likes...
Source: Google Online Security Blog
Kaisen Linux | The distribution for professional IT

Kaisen Linux is a distribution dedicated for IT professional based on Debian GNU/Linux. Large tools are integrated for diagnostics, rescue system and networks, lab creation and many more!

Kaisen Linux | The distribution for professional IT...
Kaisen Linux is a distribution dedicated for IT professional based on Debian GNU/Linux....
Google Trust Services now offers TLS certificates for Google Domains customers

Andy Warner, Google Trust Services, and Carl Krauss, Product Manager, Google DomainsWe're excited to announce changes that make getting Google Trust Services TLS certificates easier for Google Domains customers. With this integration, all Google Domains customers will be able to acquire public certificates for their websites at no additional cost, whether the site runs on a Google service or uses another provider. Additionally, Google Domains is now making an API available to allow for DNS-01 challenges with Google Domains DNS servers to issue and renew certificates automatically.Like the existing Google Cloud integration, Automatic Certificate Management Environment (ACME) protocol is used to enable seamless automatic lifecycle management of TLS certificates. These certificates are issued by the same Certificate Authority (CA) Google uses for its own sites, so they are widely supported across the entire spectrum of devices used to access your services.How do I use it?Using ACME ensures your certificates are renewed automatically and many hosting services already support ACME. If you're running your own web servers / services, there are ACME clients that integrate easily with common servers. To use this feature, you will need an API key called an External Account Binding key. This enables your certificate requests to be associated with your Google Domains account. You can get an API key by visiting Google Domains and navigating to the Security page for your domain. There you'll see a section for Google Trust Services where you can get your EAB Key.Example of EAB Credentials in Google DomainsAs an example, with the popular Certbot ACME client, the configuration to register an account looks like:certbot register --email <CONTACT_EMAIL> --no-eff-email --server "https://dv.acme-v02.api.pki.goog/directory" --eab-kid "<EAB_KEY_ID>" --eab-hmac-key "<EAB_HMAC_KEY>"The EAB_KEY_ID and EAB_HMAC_KEY are both provided on your Google Domains security page.After the account is created, you may issue certificates by running:certbot certonly -d <domain.com> --server "https://dv.acme-v02.api.pki.goog/directory" --standaloneThen follow the prompts to complete validation and download your certificate. If you need additional information please visit the Google Domains help center.Google Domains and ACME DNS-01ACME uses challenges to validate domain control before issuing certificates. The ACME DNS-01 challenge can be an efficient way for users to automate the validation process and integrate with existing websites and web hosting services.Google Domains now provides an API for ACME DNS-01 challenges that helps streamline the process for users to authenticate domain control quickly and securely. This is now offered in some popular ACME clients like Certbot via this plugin, Caddy, Certify The Web, Posh-ACME. You can find additional information on the Google Domains site.Example of DNS API Access Token in Google DomainsTo set up automatic certificate provisioning with ACME and DNS-01, follow these steps:Sign in to Google Domains.Select the domain that you want to use.At the top left, click “Menu” and select “Security”.Under section “ACME DNS API”, click “Create token”.A dialog box will appear with an “API Token”. This is the API Token you will need to enter into your ACME client. You will need to copy this value and can do so by clicking the copy button next to the API Token. NOTE: This value is only shown once. After the dialog box is closed you will not be able to see this API Token again. Store this token in a safe place, since anyone that has it gains the ability to modify some DNS TXT records for your Domain. If you did not save this value before closing the dialog box, you can easily delete and create a new API token.A limit of 10 API tokens per domain can exist at a time. Once the dialog box is closed you will be able to see in the list that the token has been created. You can delete this token at any time to revoke its access. The API token can now be used in an ACME client that supports the Google Domains ACME DNS API. Each ACME client differs slightly on how to specify this API Token so you will need to read the documentation on your desired ACME client. Regardless of which ACME client you use, Google Domains and Google Trust Services are excited to offer a reliable option for no-cost TLS certificates. This continues the mission of helping build a safer internet by providing a transparent, trusted, and reliable Certificate Authority.

Google Trust Services now offers TLS certificates...
Andy Warner, Google Trust Services, and Carl Krauss, Product Manager, Google DomainsWe're...
Source: Google Online Security Blog